Social Media Forensics & SOCMINT 2026
Social Media Forensics 2026: SOCMINT as Your Most Powerful Evidence Layer In 2023, a suspect in a high-profile fraud ca...
Stay ahead of cyber threats with expert insights, breaking news, and practical guides tailored specifically for the Cyber Security landscape.
Join 5,000+ subscribers. No spam, unsubscribe anytime.
Deep dives into the latest security trends. (173 articles)
Social Media Forensics 2026: SOCMINT as Your Most Powerful Evidence Layer In 2023, a suspect in a high-profile fraud ca...
Agentic AI in DFIR 2026: When the Investigator Never Sleeps At 2:47 AM, a ransomware payload begins lateral movement ac...
Webworm EchoCreep & GraphWorm: Discord and Graph API as Spy Channels When your SIEM alerts on suspicious C2 traffic, it...
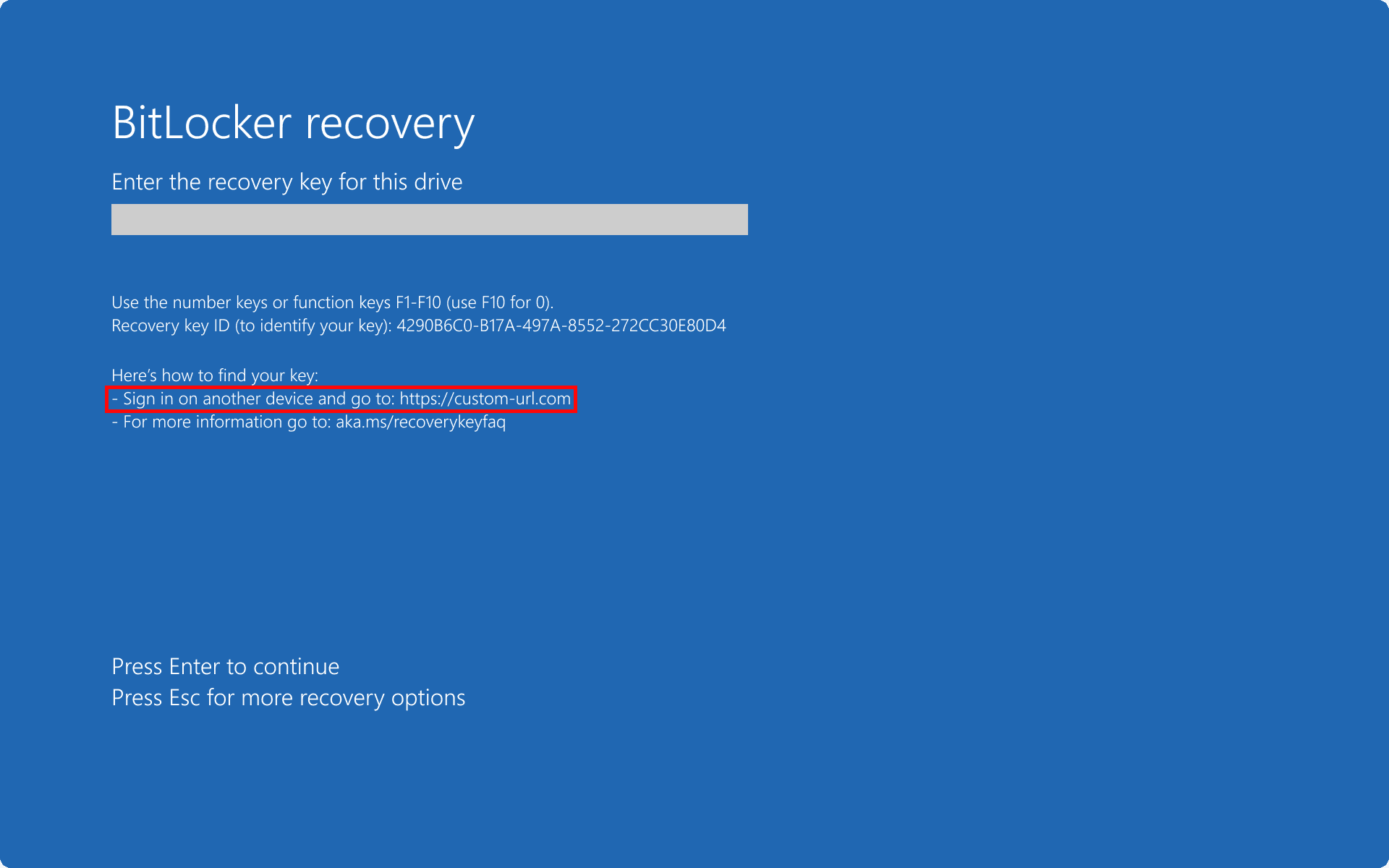
YellowKey CVE-2026-45585: BitLocker Bypass With a USB Drive and a Reboot Physical access to a Windows machine is not su...
SonicWall CVE-2024-12802: Why "Patched" Still Means Vulnerable in 2026 Your SonicWall Gen6 SSL-VPN device shows the lat...
GitHub Breach 2026: How TeamPCP Stole 3,800 Internal Repositories On May 20, 2026, GitHub — the platform that hosts the...
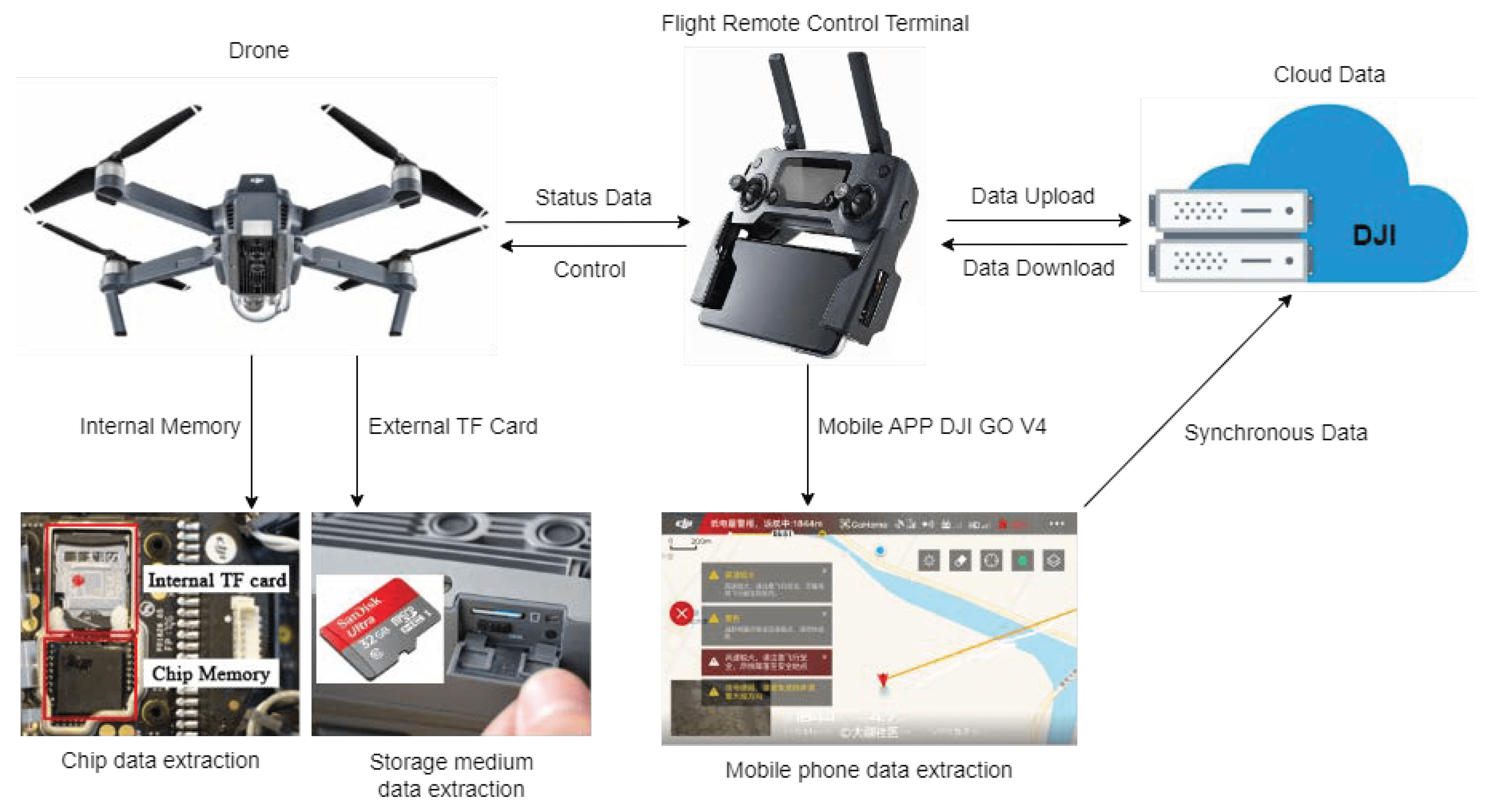
Drone Forensics 2026: Extracting Digital Evidence From Unmanned Aerial Vehicles A DJI Mavic 3 was intercepted near a cl...
Microsoft Teams MFA Theft 2026: How MuddyWater Built a False Flag Operation Your employees trust Microsoft Teams. They...
OpenAI Daybreak 2026: AI Rewrites the Vulnerability Detection Playbook The 90-day coordinated disclosure window — the s...
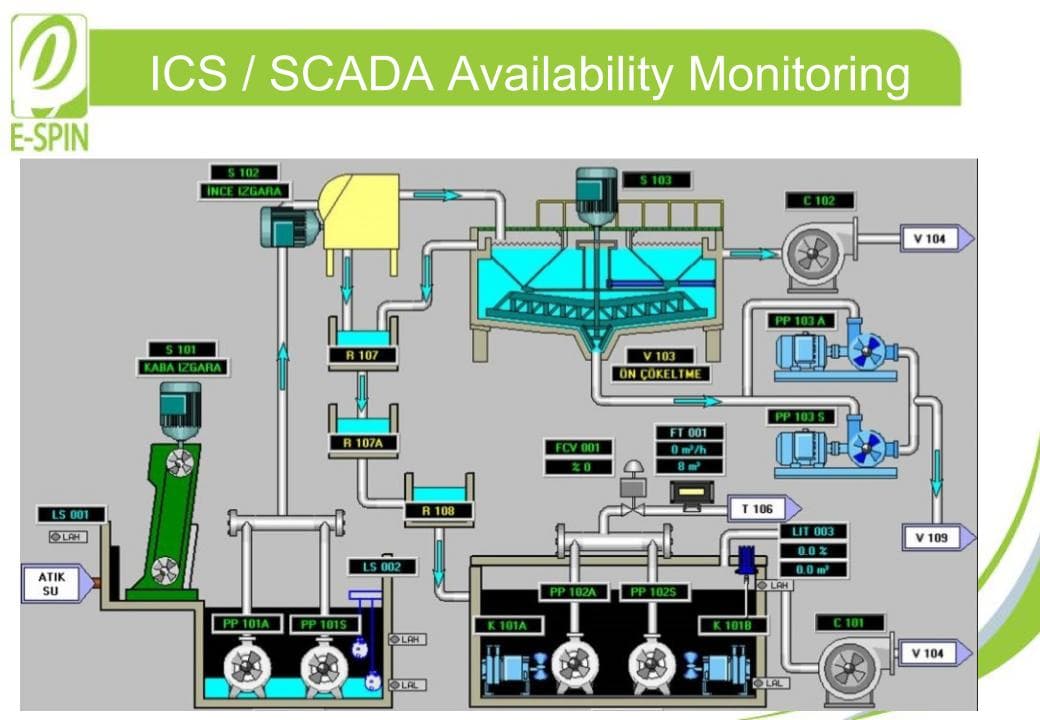
OT/ICS/SCADA Forensics 2026: Investigating Breaches in Critical Infrastructure A cyberattack on an operational technolo...

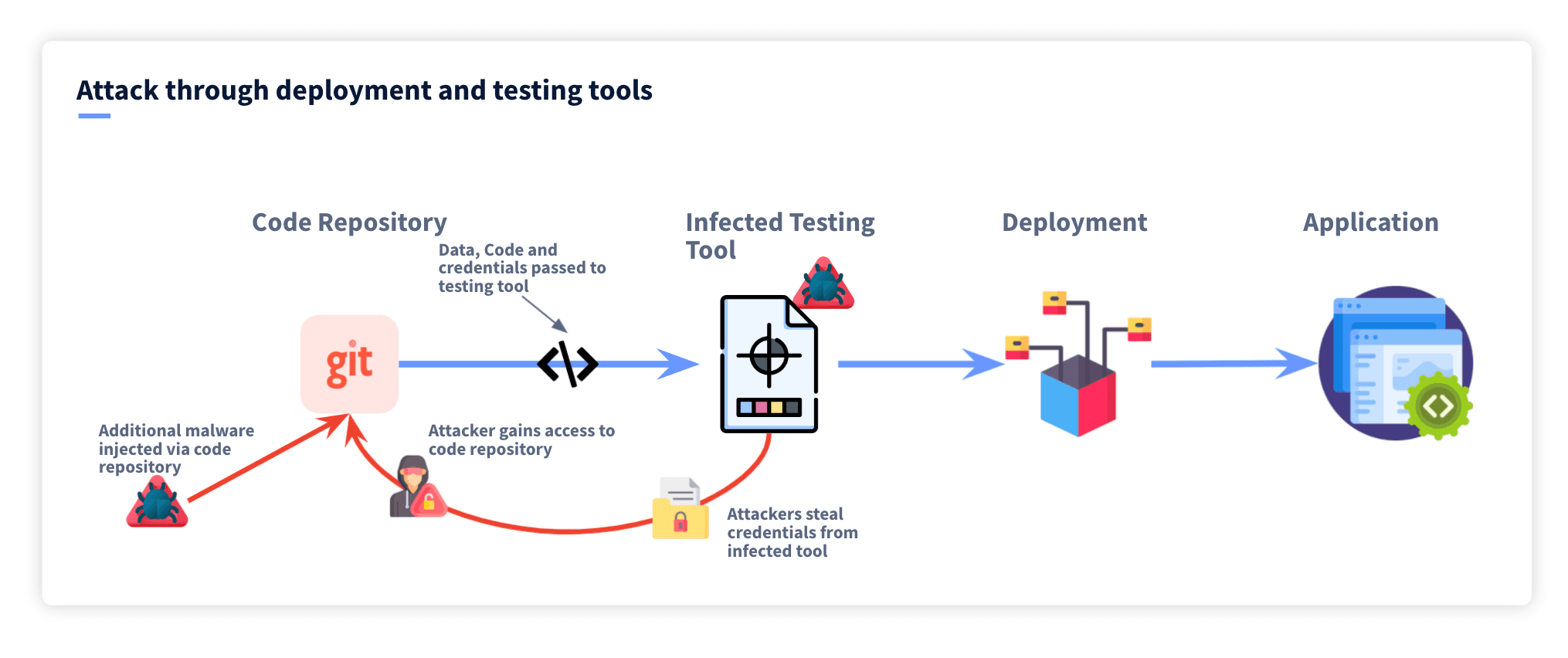
Software Supply Chain Forensics 2026: Investigating the Breach Behind the Breach On March 23, 2026, attackers compromis...
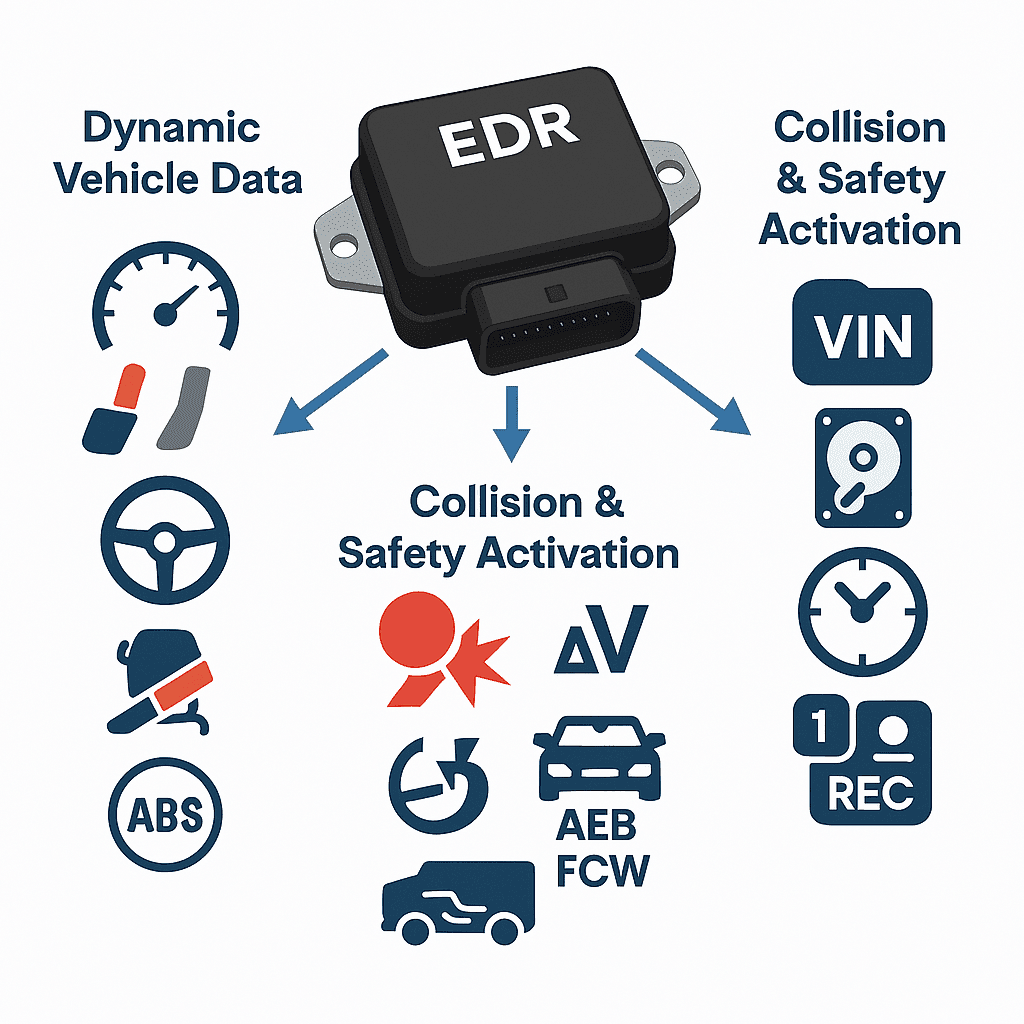
Automotive Forensics 2026: Extracting Digital Evidence From Connected Vehicles A vehicle's onboard systems recorded the...