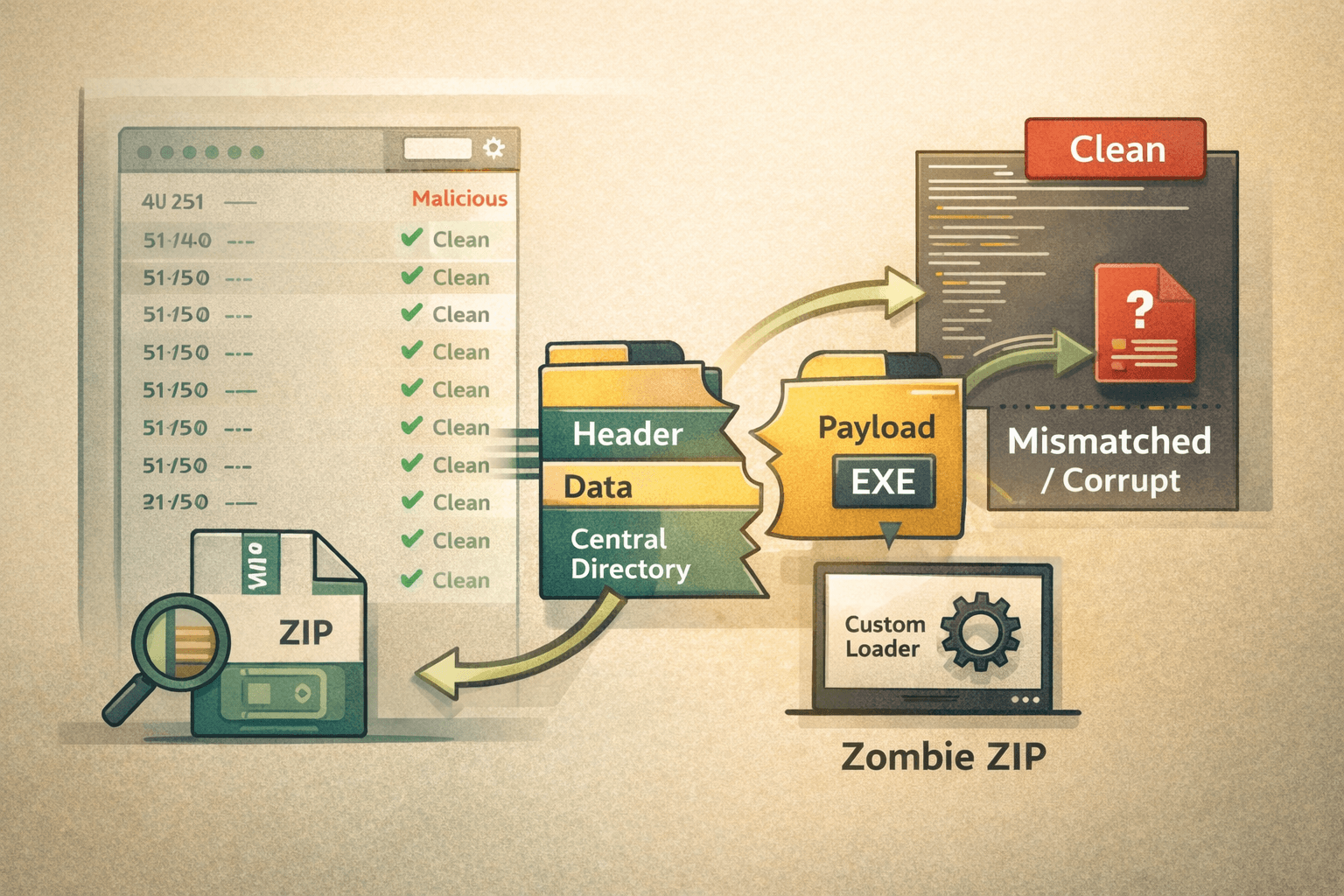
A single malicious file bypassed 50 out of 51 antivirus engines on VirusTotal. No zero-day exploit. No nation-state tooling. Just a carefully malformed ZIP archive and a fundamental assumption that defenders have trusted for years — that what a security scanner sees inside a compressed file is what actually executes.
That assumption is now broken. Researcher Chris Aziz published proof-of-concept (PoC) archives demonstrating Zombie ZIP, a technique that manipulates ZIP file headers to force a split between what security tools scan and what a custom loader actually extracts and runs. CERT/CC has since urged vendors to validate compression metadata against actual file content rather than trusting header fields at face value.
This article explains how Zombie ZIP works at a technical level, why existing detection stacks struggle to catch it, what the realistic threat model looks like for enterprise environments, and what detection engineers, AppSec teams, and gateway administrators can do today to reduce exposure.
How Zombie ZIP Manipulates Archive Structures
To understand why Zombie ZIP works, you need to understand how ZIP parsers read archives — and why different implementations make different trust decisions about header fields.
The ZIP Format's Trust Problem
A ZIP archive contains two critical data structures: Local File Headers (LFH) at the start of each compressed entry, and the Central Directory (CD) at the end of the archive. Most security scanners rely heavily on the Central Directory because it provides an index of all entries without requiring full sequential parsing. This is a deliberate performance optimization — scanning the entire compressed stream on every file would be prohibitively slow.
Zombie ZIP exploits the gap between these two structures. By manipulating the compression method field in the Local File Header — specifically by marking compressed data as uncompressed — the technique causes security engines to attempt to scan raw compressed bytes as if they were plaintext content. The actual payload is invisible to the scanner because it is looking at the wrong representation of the data.
The manipulated fields that drive this technique include:
- Compression method byte — set to
0x00(stored/uncompressed) while actual data remains deflate-compressed - Compressed size field — misreported to misdirect parser offsets
- CRC-32 checksum — forged to prevent integrity failure during the scanner's parse pass
- General-purpose bit flag — selectively modified to influence parser behavior across different implementations
What Standard Tools See vs. What Executes
Standard archive utilities — including WinRAR and 7-Zip — correctly detect the inconsistency between the header fields and the actual compressed data. They display errors or corruption warnings when users attempt to open a Zombie ZIP manually. This behavior looks, on the surface, like a detection signal. It is not.
Security scanning engines process archives differently from interactive archive clients. Many engines encounter the malformed header, attempt to parse the content using the stated compression method, retrieve what appears to be garbled or empty data, and flag the file as either clean or unreadable-but-benign. Neither outcome triggers a malware alert.
A custom loader — written specifically to ignore the forged header fields and apply the correct decompression algorithm to the raw byte stream — extracts and executes the payload without error. The attacker controls both the malformed archive and the loader. The defender's scanner controls neither.
Table: How Different Parsers Handle a Zombie ZIP Archive
| Parser Type | Behavior | Security Outcome |
|---|---|---|
| Security scanner (most) | Reads forged header, scans wrong data | File appears benign |
| WinRAR / 7-Zip | Detects header inconsistency, shows error | User sees corruption warning |
| Custom attacker loader | Ignores header, applies correct decompression | Payload executes successfully |
| Correctly hardened scanner | Validates metadata against actual data | Detects anomaly |
Why Existing Detection Stacks Fail Against This Technique
The 50-of-51 bypass rate on VirusTotal is not a coincidence — it reflects a structural assumption baked into most archive scanning logic. Understanding why scanning engines fail here is essential for prioritizing where to invest detection engineering effort.
Signature and Hash-Based Detection Gaps
Traditional antivirus detection relies on matching file content against known-bad signatures or hashes. Zombie ZIP defeats this approach in two ways. First, the payload bytes are never presented to the scanner in their executable form — they appear as compressed data misidentified as plaintext. Second, because the technique is a format manipulation primitive rather than a specific payload, there is no single signature that covers it. Any payload, delivered inside any Zombie ZIP-formatted archive, passes through unseen.
This maps directly to MITRE ATT&CK T1027.013 (Obfuscated Files or Information: Encrypted/Encoded File) and T1140 (Deobfuscate/Decode Files or Information), though the specific header manipulation represents a novel sub-variant that existing ATT&CK coverage does not fully describe.
Email and File Gateway Blind Spots
Mail security gateways and web proxies that perform content inspection face the same parsing problem as endpoint antivirus engines. An email attachment or downloaded file that a gateway classifies as a corrupt-but-clean archive passes directly to the endpoint. If the endpoint scanner uses the same parser logic — which is common when both products consume the same underlying archive library — no layer of the defense-in-depth stack catches the file.
Important: Organizations that rely on gateway scanning as a primary control for malicious attachments should treat Zombie ZIP as a current, active bypass until their gateway vendor publishes a patch or detection update explicitly addressing header validation for ZIP Central Directory versus Local File Header inconsistencies.
Sandbox and Dynamic Analysis Limitations
Behavioral sandboxes that execute suspicious files to observe runtime behavior represent a stronger control against this technique — but only if the sandbox's detonation environment uses a loader capable of correctly extracting the payload. A sandbox that attempts to open the archive using a standard library may encounter the same extraction failure that WinRAR displays to end users. If the payload never executes inside the sandbox, no behavioral indicators generate.
Table: Detection Method Effectiveness Against Zombie ZIP
| Detection Method | Effectiveness | Reason |
|---|---|---|
| Signature-based AV | Very Low | Payload bytes never presented correctly |
| Hash matching | None | Each archive is uniquely crafted |
| Gateway content inspection | Very Low | Same parser flaw as endpoint AV |
| Behavioral sandbox (standard loader) | Low | Payload may not detonate |
| Behavioral sandbox (custom loader) | Moderate | Depends on loader implementation |
| Header validation / structural analysis | High | Directly detects the manipulation |
| YARA rules targeting LFH/CD mismatch | High | Effective for tuned detection engineering |
Detection Engineering Responses to Zombie ZIP
The path forward for detection engineers is clear in principle, though it requires updating assumptions that have been stable for years. Catching Zombie ZIP requires detecting the structural anomaly in the archive itself, not the payload it contains.
YARA Rules Targeting Header Inconsistencies
The most immediately actionable detection approach is writing YARA rules that identify mismatches between the compression method field in Local File Headers and the corresponding entry in the Central Directory. A legitimate ZIP archive — produced by any standard tool — will have consistent compression metadata across both structures. A Zombie ZIP archive will not.
Key detection logic to encode in YARA or similar rules:
- Flag archives where LFH compression method (
0x0000) contradicts CD compression method (0x0008for deflate) - Alert on archives where CRC-32 values in LFH do not match actual decompressed content hashes
- Detect unusually large discrepancies between stated and actual compressed sizes
- Flag archives that generate extraction errors in standard libraries but contain non-empty byte streams
Updating Gateway and AV Vendor Parsers
CERT/CC's advisory to vendors is direct: archive parsers must validate compression metadata against actual compressed data rather than trusting header fields unconditionally. For detection and IR teams, this translates to a vendor communication task — contact your gateway and endpoint vendors to ask specifically whether they have implemented Central Directory versus Local File Header consistency validation. If they have not, treat ZIP-based email attachments and downloads as higher risk until they do.
Pro Tip: When evaluating vendor responses to Zombie ZIP, ask specifically whether their scanner independently parses both the Local File Header and the Central Directory and cross-validates compression method fields. A general "we've updated our detection" response without this specificity is insufficient.
Network and Endpoint Monitoring
While signature-based controls catch up, behavioral monitoring at the endpoint provides a detection layer that does not depend on archive parser correctness:
- Alert on processes that spawn from archive extraction utilities and immediately attempt code execution
- Monitor for
cmd.exe,powershell.exe, or script interpreter processes whose parent is an archive handler - Flag outbound network connections initiated within seconds of an archive being written to disk
- Detect processes reading raw archive byte streams using custom file I/O patterns inconsistent with standard library calls
Compliance and Risk Implications for Enterprise Environments
Zombie ZIP's near-universal AV bypass has direct implications for organizations operating under regulatory frameworks that require demonstrable malware detection controls.
Framework Alignment and Gaps
Table: Compliance Framework Controls Affected by Zombie ZIP
| Framework | Relevant Control | Gap Created |
|---|---|---|
| NIST CSF 2.0 | DE.CM-5: Detect unauthorized software | AV bypass undermines detection coverage |
| CIS Controls v8 | Control 10: Malware Defenses | Signature-based tools insufficient alone |
| ISO 27001 | A.12.2: Protection from malware | Policy-level controls require technical update |
| PCI DSS v4.0 | Req 5: Protect against malicious software | Antivirus adequacy assumption challenged |
| SOC 2 Type II | CC6.8: Prevent unauthorized software | Evidence of detection gaps affects audit posture |
Organizations undergoing SOC 2 Type II audits or PCI DSS assessments should document Zombie ZIP as a known detection gap in their risk register until vendor patches are available. Demonstrating awareness and compensating controls — such as behavioral monitoring and enhanced gateway logging — is more defensible than silence.
Key Takeaways
- Treat ZIP-based attachments as elevated risk until your gateway and endpoint vendors confirm they validate LFH compression fields against Central Directory metadata
- Write or acquire YARA rules targeting Local File Header and Central Directory compression method mismatches — this structural anomaly is detectable without payload signatures
- Test your sandbox environment against published Zombie ZIP PoC archives to determine whether your detonation environment correctly extracts and executes the payload
- Contact endpoint and gateway vendors with a specific question about header consistency validation, not a general inquiry about the technique
- Document the detection gap in your risk register under CIS Control 10 or equivalent framework control, with compensating controls noted
- Layer behavioral monitoring — parent-process chains from archive handlers, rapid network connections post-extraction — as a compensating control while parser updates roll out
Conclusion
Zombie ZIP is not a payload or a family of malware. It is a detection-evasion primitive — a reusable technique that any attacker can apply to any payload to bypass the majority of current antivirus and gateway scanning infrastructure. That distinction matters because patching against a primitive requires changing how scanners fundamentally trust archive metadata, not simply adding a new signature.
The 50-of-51 VirusTotal bypass rate should be read as a stress test result for the archive parsing assumptions your entire detection stack currently makes. Until vendors implement Central Directory versus Local File Header cross-validation, behavioral detection and structural YARA rules are your most reliable compensating controls.
Start by testing your sandbox against the published PoC archives. Then ask your vendors the right questions. The answers will tell you exactly how exposed your environment is right now.
Frequently Asked Questions
Q: Does Zombie ZIP affect all ZIP-based file formats, including DOCX and XLSX?
A: Office Open XML formats like DOCX and XLSX are ZIP archives at their core, which means the same header manipulation technique is theoretically applicable. However, Office application parsers and document security scanners use different code paths than general-purpose archive handlers, so the bypass effectiveness may vary. Organizations should test their document security controls against Zombie ZIP-formatted Office files specifically.
Q: Can endpoint detection and response (EDR) tools catch Zombie ZIP where AV fails?
A: EDR tools with strong behavioral analysis capabilities — particularly those monitoring process lineage and post-extraction execution chains — have a better chance of catching Zombie ZIP payloads at execution time than signature-based AV. However, EDR tools that rely on archive scanning as a pre-execution filter face the same parser flaw. The key question for your EDR vendor is whether their archive inspection validates header metadata or trusts it.
Q: How quickly are antivirus vendors expected to patch for Zombie ZIP?
A: CERT/CC's coordinated disclosure means most major vendors are aware of the technique and working on parser updates. However, implementing correct Central Directory versus Local File Header validation requires changes to core archive parsing libraries that may affect performance and backward compatibility. Patch timelines will vary by vendor. Monitor vendor security advisories and test your specific tools against PoC archives rather than assuming coverage.
Q: Is there a way to block Zombie ZIP at the email gateway without parser updates?
A: A blunt but effective compensating control is to block or quarantine all inbound ZIP archives pending manual review or sandboxed detonation by a human analyst. This is operationally expensive but eliminates the parsing gap. A more targeted option is to flag any ZIP archive that generates extraction errors in standard libraries — the corruption warning that WinRAR and 7-Zip display is a detectable signal that gateway rules can act on.
Q: Does encrypting ZIP archives change the Zombie ZIP risk profile?
A: Password-protected or encrypted ZIP archives present their own scanning challenges — security tools generally cannot inspect their contents without the key — but Zombie ZIP operates on the archive structure itself, not the encryption layer. An encrypted Zombie ZIP would combine two separate detection-evasion techniques. Detection engineering teams should account for this combination when writing detection logic, as encrypted archives with structural anomalies in their unencrypted headers represent a meaningful escalation in risk.
Enjoyed this article?
Subscribe for more cybersecurity insights.
