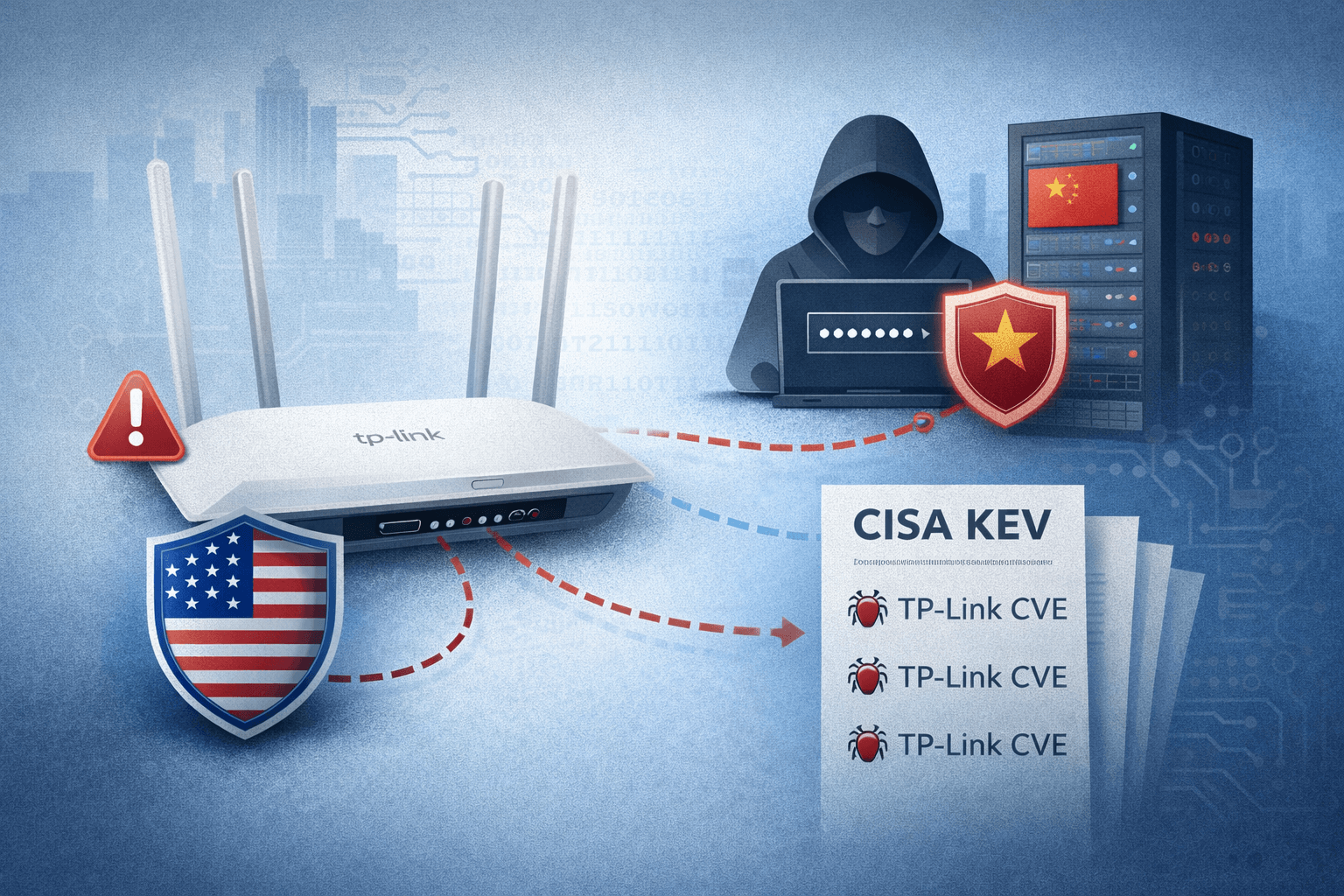
A single router sitting in your server room or branch office could be the entry point for a nation-state attack. That is no longer a hypothetical. In 2024 and 2025, TP-Link devices became a focal point for some of the most significant supply-chain security concerns in recent memory — and now the legal system is catching up.
The Texas Attorney General has filed suit against TP-Link, alleging the company made false claims about device security while maintaining undisclosed data flows to servers in China. Meanwhile, the Cybersecurity and Infrastructure Security Agency (CISA) has added multiple TP-Link vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, confirming active exploitation in the wild.
If your organization runs TP-Link hardware — in the office, at remote sites, or across a managed network — this situation demands your immediate attention. This post breaks down the legal action, the technical vulnerabilities, the threat actor activity, and the practical steps you should take right now to reduce your exposure.
The Texas AG Lawsuit: What the Allegations Actually Mean
The Texas Attorney General's lawsuit against TP-Link centers on a specific and serious claim: that the company marketed its devices as secure and free of backdoors while evidence suggests otherwise. The suit demands full disclosures on how user data flows to servers outside the United States, specifically to infrastructure tied to China.
This is not a routine consumer protection case. It represents a growing regulatory posture that treats IoT (Internet of Things) hardware vendors as accountable actors in the national security supply chain.
The "No Backdoors" Claim Under Scrutiny
TP-Link has publicly stated that its devices contain no backdoors. Researchers and government investigators have challenged that claim. Firmware analysis has revealed hardcoded credentials, undocumented remote access capabilities, and telemetry functions that phone home to external servers — behaviors that are difficult to reconcile with a clean security posture.
The lawsuit argues that these discrepancies constitute deceptive trade practices. For IT and security professionals, the more immediate concern is operational: if firmware behavior is not what the vendor claims, your network segmentation and access control assumptions may be wrong.
Regulatory Parallels: The China IoT Ban Effort
The Texas suit does not exist in isolation. It mirrors federal-level efforts to restrict Chinese-manufactured networking equipment from critical infrastructure. The FCC has moved to limit Huawei and ZTE equipment. Congressional proposals have targeted routers from Chinese vendors more broadly.
Table: Key Regulatory Actions Targeting Chinese IoT Hardware
| Action | Body | Year | Scope |
|---|---|---|---|
| FCC Equipment Authorization Ban | FCC | 2022–2023 | Huawei, ZTE, Dahua, Hikvision |
| NDAA Section 889 | U.S. Congress | 2019 | Federal procurement restrictions |
| Texas AG Lawsuit vs TP-Link | Texas AG | 2024–2025 | Consumer/SMB router deception claims |
| CISA KEV Listings | CISA | 2024–2025 | Active exploitation disclosures |
| Congressional Router Inquiry | House Committee | 2024 | TP-Link market share investigation |
Firmware Vulnerabilities and Active Exploitation
Beyond the legal allegations, the technical record is damning on its own. CISA's KEV catalog — which lists vulnerabilities confirmed to be actively exploited — includes multiple TP-Link CVEs (Common Vulnerabilities and Exposures). These are not theoretical risks. Threat actors are using them now.
Botnets and State-Sponsored Activity
Firmware flaws in TP-Link devices have been exploited to recruit routers into botnets controlled by state-sponsored actors. Microsoft and other threat intelligence firms have attributed some of this activity to a Chinese threat group tracked as Volt Typhoon. This group has specifically targeted U.S. critical infrastructure, using compromised routers as covert relay nodes to obscure the origin of intrusion traffic.
Botnet recruitment via router firmware exploits is particularly dangerous because infected devices continue to function normally from the user's perspective. Your router passes traffic, your users browse the web, and in the background, the device participates in reconnaissance or credential theft operations targeting other networks.
Credential Theft via Router Compromise
Compromised routers sit in an ideal position for credential harvesting. They can intercept unencrypted traffic, manipulate DNS (Domain Name System) responses to redirect users to phishing infrastructure, and perform man-in-the-middle attacks against insufficiently protected sessions.
Important: Even organizations using HTTPS extensively remain at risk if router-level DNS manipulation redirects users before TLS (Transport Layer Security) sessions are established.
Patch Gaps and Remote Exploit Windows
TP-Link has faced consistent criticism for slow patch cycles. Security researchers have reported responsible disclosure timelines stretching months without remediation — leaving known vulnerabilities open for exploitation long after they become public. For remote code execution (RCE) vulnerabilities, that window is unacceptable.
Table: TP-Link Vulnerability Risk Profile
| Vulnerability Type | Attack Vector | Patch Timeline | Exploitation Status |
|---|---|---|---|
| Remote Code Execution | Network | Slow (60–180+ days) | Confirmed (CISA KEV) |
| Hardcoded Credentials | Network/Physical | Inconsistent | Confirmed |
| Authentication Bypass | Network | Variable | Confirmed |
| Telemetry Data Exfiltration | Network | Disputed | Under investigation |
| DNS Hijacking via Firmware | Network | Variable | Suspected |
Nation-State Router Compromises: Understanding the Threat Model
Volt Typhoon's use of compromised routers as operational relay infrastructure represents a mature, patient threat strategy. Rather than conducting attacks directly from known infrastructure — which defenders can block — state actors route intrusion traffic through legitimate-looking residential and small business routers.
Why Routers Are the Perfect Pivot Point
Routers rarely receive the same security scrutiny as endpoints and servers. They often run outdated firmware indefinitely. Security Operations Centers (SOCs) frequently lack visibility into router-level telemetry. Intrusion Detection Systems (IDS) positioned inside the network perimeter see internal traffic, not the command-and-control (C2) communications happening at the router itself.
This visibility gap makes routers ideal for adversaries seeking persistent, low-noise footholds in target environments.
MITRE ATT&CK Relevance
The MITRE ATT&CK framework documents several techniques directly relevant to router-based compromises. Adversaries use T1584.008 (Compromise Infrastructure: Network Devices) to establish proxy infrastructure. They leverage T1557 (Adversary-in-the-Middle) for credential interception. Understanding these tactics helps defenders build detection logic even when router telemetry is limited.
Pro Tip: Map your network device inventory against MITRE ATT&CK's network device compromise techniques. If you cannot detect these behaviors at the router layer, your detection coverage has a significant gap.
Practical Defense: What Your Organization Should Do
Understanding the threat is necessary. Acting on it is essential. Regardless of how the legal proceedings against TP-Link conclude, the technical exposure is real and addressable today.
Firmware Audits and Inventory Control
Start with a complete inventory of network hardware across all sites, including remote offices, branch locations, and any equipment managed by third-party MSPs (Managed Service Providers). Identify every TP-Link device and cross-reference its firmware version against current releases and known CVEs.
For devices running outdated firmware with available patches, update immediately. For devices with no available patches for known exploited vulnerabilities, treat them as compromised and plan replacement.
VLAN Segmentation as a Containment Strategy
Network segmentation using VLANs (Virtual Local Area Networks) limits the blast radius of a compromised router. If a device at your network edge is recruited into a botnet or used as a pivot point, proper segmentation prevents lateral movement into your core infrastructure.
- Isolate IoT devices on dedicated VLANs with strict ACLs (Access Control Lists)
- Segment guest networks completely from corporate traffic
- Restrict management interfaces to out-of-band networks
- Log all inter-VLAN routing for anomaly detection
- Apply zero-trust principles to east-west traffic
Monitoring and Detection Enhancements
Deploy network flow analysis tools capable of detecting unusual outbound traffic patterns from edge devices. Routers that suddenly initiate high-volume connections to unfamiliar external IPs, or that exhibit unusual DNS query patterns, may be compromised.
Table: Detection Indicators for Compromised Routers
| Indicator | Normal Behavior | Suspicious Behavior | Action |
|---|---|---|---|
| Outbound Connections | Known ISP/CDN IPs | Unknown foreign IPs | Investigate immediately |
| DNS Queries | Internal resolver | External resolver change | Audit DNS config |
| Firmware Hash | Matches vendor release | Mismatch detected | Isolate device |
| Management Logins | Scheduled admin activity | Off-hours access | Alert and review |
| Traffic Volume | Consistent baseline | Sudden spike | Run flow analysis |
Key Takeaways
- Audit your hardware inventory immediately — identify every TP-Link device and its current firmware version before doing anything else
- Treat CISA KEV listings as mandatory action items — if a vulnerability is listed and your device is unpatched, exploitation is a matter of when, not if
- Implement VLAN segmentation to contain any compromise at the network edge before it reaches critical systems
- Build router-level visibility into your SOC monitoring — blind spots at the network edge are exactly what nation-state actors exploit
- Apply supply-chain scrutiny to hardware procurement — evaluate vendor transparency, patch cadence, and country of origin as part of your purchasing criteria
- Reference NIST SP 800-189 and CIS Controls v8 for guidance on network device hardening and router security baselines
Conclusion
The TP-Link situation is not simply a legal dispute or a political story about U.S.-China relations. It is a concrete, technically grounded warning about the risks of treating network hardware as a commodity purchase rather than a security decision.
Millions of TP-Link devices sit inside home offices, small businesses, and enterprise branch locations across the United States. Each one represents a potential entry point for the threat actors and exploitation techniques described in this post. The combination of unpatched firmware, alleged deceptive security claims, and confirmed state-sponsored exploitation makes this a high-priority issue for any security-conscious organization.
Your next step is straightforward: run your hardware inventory, check your firmware versions against CISA's KEV catalog, and assess your network segmentation posture. The threat is active. The evidence is public. The response is yours to execute.
Frequently Asked Questions
Q: Are TP-Link routers banned in the United States? A: As of 2025, TP-Link routers are not subject to a federal ban for general consumers or businesses. However, CISA has listed multiple TP-Link vulnerabilities as actively exploited, and congressional inquiries have examined the company's market position and potential national security implications.
Q: What does the CISA KEV catalog mean for my organization? A: The KEV catalog lists vulnerabilities that CISA has confirmed are being actively exploited in the wild. Federal agencies are required to patch KEV-listed vulnerabilities within strict deadlines. For private organizations, KEV listings should function as high-priority remediation triggers, not optional guidance.
Q: How can I tell if my router has been compromised by a botnet? A: Common indicators include unusual outbound traffic to unfamiliar IP addresses, unexpected changes to DNS settings, degraded performance without explanation, and unauthorized firmware modifications. Network flow analysis and regular firmware hash verification are your most reliable detection methods.
Q: What is Volt Typhoon and why does it matter for router security? A: Volt Typhoon is a Chinese state-sponsored threat group that has specifically targeted U.S. critical infrastructure. The group uses compromised routers — including residential and SMB devices — as relay nodes to conduct intrusions while obscuring the origin of their traffic. This technique makes attribution and blocking significantly harder for defenders.
Q: What should I do if I cannot immediately replace vulnerable TP-Link hardware? A: Prioritize isolation and monitoring. Place vulnerable devices on isolated VLANs with restrictive access control rules. Block management interfaces from external access. Increase logging and alerting for anomalous traffic originating from those devices. Document the risk formally and accelerate your replacement timeline as a business priority.
Enjoyed this article?
Subscribe for more cybersecurity insights.
