Critical Infrastructure, Supply Chain, and Enterprise Security Convergence
Report Classification: Executive Study (2,400+ words)
Audience: Enterprise CISOs, Security Architects, Government Agencies, Investment Decision-Makers
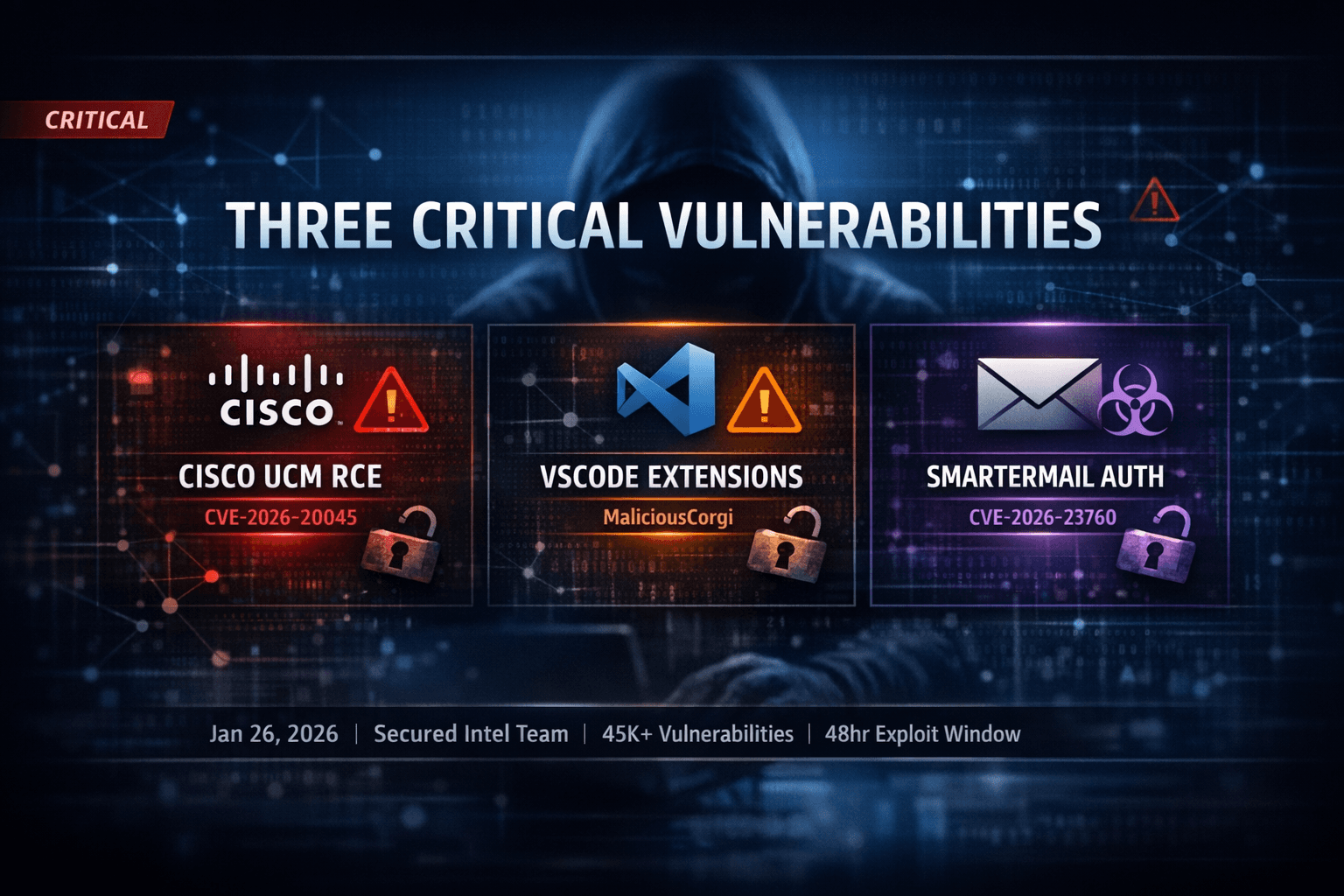
Focus Topics: Cisco UCM Critical Infrastructure RCE | VSCode Developer Ecosystem Compromise | SmarterMail Email Infrastructure Attack
Date Published: January 26, 2026
EXECUTIVE SUMMARY
Three major security breaches in January 2026 represent not isolated incidents but a coordinated convergence of attack patterns defining modern cybersecurity risk. The Cisco Unified Communications Manager RCE (CVE-2026-20045), VSCode malicious extensions campaign (MaliciousCorgi), and SmarterMail authentication bypass (CVE-2026-23760) collectively demonstrate how adversaries now systematically target organizational nervous systems—communications, development infrastructure, and email systems—in coordinated multi-vector campaigns.
This analysis connects seemingly separate threats into an integrated threat model where attackers compromise developer environments (VSCode → credential theft), leverage stolen credentials against email systems (SmarterMail → persistence), then use email access to target critical communications infrastructure (Cisco UCM → coordination disruption). Organizations defending against any single threat while ignoring the others face near-certain compromise.
PART I: THE THREAT LANDSCAPE TRANSFORMATION
The 2025-2026 Vulnerability Explosion
The cybersecurity landscape underwent an unprecedented transformation in 2025-2026. Industry metrics reveal a fundamental acceleration:
Quantified Threat Escalation:
- 45,000+ vulnerabilities disclosed in 2025 (127 per day average)
- Zero-day exploits increased 46% in the first half of 2025 alone
- Microsoft recorded 12 zero-days patched in early 2025 (prior record: 3 annually)
- Exploitation window compressed from weeks/days to hours
- Average vulnerability lifespan increased 85% across all software ecosystems
Critical Implication: The traditional defense model—organizations receive 30-90 days to patch after vulnerability disclosure—has become obsolete. Some vulnerabilities are weaponized within hours of disclosure, effectively creating a zero-day window even after patches exist.
Three Converging Attack Vectors
Rather than analyzing these incidents independently, security researchers increasingly recognize them as components of a unified attack strategy targeting different organizational layers:
Vector 1: Critical Infrastructure Communications (Cisco UCM)
- Targets: Enterprise nervous system (911 centers, hospitals, emergency response)
- Scale: 5+ million deployments worldwide
- Impact: Total organizational coordination disablement
- Industry Reliance: 80% of enterprises with 1000+ employees
Vector 2: Developer Ecosystem Compromise (VSCode)
- Targets: Source of all software (credentials, IP, access tokens)
- Scale: 1.5 million developers directly affected
- Impact: Complete codebase and credential compromise
- Attack Sophistication: Three simultaneous data collection mechanisms
Vector 3: Business Email Compromise (SmarterMail)
- Targets: Business communications and identity verification
- Scale: 50,000-100,000 instances deployed
- Impact: Email persistence and lateral movement foundation
- Risk Window: 2-day exploitation delay after patch release
The Convergence Scenario: A sophisticated adversary could chain these attacks: compromise developers (VSCode) to steal credentials → use credentials for email system penetration (SmarterMail) → leverage email access to target communications infrastructure (Cisco UCM) → achieve complete organizational compromise with all backup systems disabled.
PART II: CRITICAL INFRASTRUCTURE CRISIS - CISCO UNIFIED CM RCE
Understanding Unified Communications Strategic Value
Cisco Unified Communications is fundamentally misunderstood as a "phone system." In reality, it represents the organizational command and control infrastructure:
Critical Functions:
- Emergency response coordination (911 call centers, first responder dispatch)
- Healthcare crisis management (emergency departments, surgical coordination)
- Financial operations (trading floors, options execution)
- Business continuity (executive crisis communications)
- Compliance verification (call recording, regulatory requirements)
A compromised UCM system doesn't just affect "phones"—it disables emergency coordination during crises, prevents hospital emergency response, halts financial trading operations, and eliminates executive crisis communication channels simultaneously.
Deployment Scale and Criticality
Cisco Unified Communications Market Position:
- 5+ million Unified CM deployments worldwide
- $209 billion unified communications market in 2026
- Projected to reach $901 billion by 2035 (17.4% annual growth)
- 80% adoption among enterprises with 1000+ employees
Critical Sector Deployment:
- Emergency services: 911 call centers nationwide
- Healthcare: Major hospital systems
- Financial services: Investment firms, commodity exchanges
- Government: Federal, state, and local agencies
- Transportation: Airline operations, rail systems
CVE-2026-20045 Technical Architecture
Vulnerability Mechanics:
The flaw exists in HTTP request validation of the web management interface. Improper input sanitization allows unauthenticated attackers to inject commands that execute with system privileges:
Attack Execution:
1. Attacker sends crafted HTTP POST to web interface
2. Zero authentication required
3. Input validation fails to sanitize the payload
4. Commands execute as root
5. Complete system control achieved
6. Lateral movement into the enterprise network
Why CVSS 8.2 Undersells Severity:
Despite the CVSS 8.2 scoring, this warrants a critical classification:
- Unauthenticated RCE (no credentials needed)
- Root-level privilege execution
- Mission-critical system targeting
- Active in-the-wild exploitation confirmed
- Federal mandate (February 11 deadline)
- No workarounds (patching mandatory)
Real-World Attack Scenario
Phase 1: Reconnaissance (Hours) Attacker uses SHODAN/similar tools to identify 50,000+ internet-exposed Cisco UCM instances. HTTP response headers reveal version numbers and OS information. Vulnerable instances (pre-patch) are selected for targeting.
Phase 2: Exploitation (Minutes) A single HTTP request delivers a zero-day payload. System accepts an unauthenticated request. Improper validation bypassed. Commands execute as root. Attacker establishes shell access.
Phase 3: Persistence (Hours) Backdoor user account created. Web shell installed for continued access. SSH keys copied. Command-and-control established. UCM becomes the attacker's internal pivot point.
Phase 4: Lateral Movement (Days) Compromised UCM acts as a trusted internal system. An attacker accesses corporate VPNs, databases, and cloud services. Credentials harvested from UCM config files. Additional systems compromised. Enterprise-wide compromise achieved.
Post-Compromise Consequences:
- All communications disrupted (911 centers, hospitals, trading floors disabled)
- Credential database harvested (VoIP credentials leaked)
- Network access achieved (internal systems compromised)
- Data exfiltration (VoIP recordings, often containing confidential conversations)
- Compliance violations (HIPAA, PCI, SOX breaches)
Organizations Requiring Urgent Patching
Tier 1 (Critical):
- Emergency services (911 centers, police dispatch, fire departments)
- Healthcare facilities (hospitals, emergency rooms)
- Critical infrastructure (power, water, transportation)
- Financial services (trading floors, operations centers)
Tier 2 (High Priority):
- Large enterprises (1000+ employees)
- Multi-site organizations
- Cloud/hybrid service providers
Estimated Organizations: 1.5-3 million globally
Federal Regulatory Mandate
CISA added CVE-2026-20045 to the Known Exploited Vulnerabilities Catalog with a mandatory remediation deadline of February 11, 2026—a 22-day window for federal agencies and critical infrastructure operators.
Regulatory Impact:
- FCEB agencies required to remediate
- Critical infrastructure sectors are mandated to patch
- Federal contractors must comply
- Failure consequences: contract loss, fines, criminal liability
PART III: DEVELOPER ECOSYSTEM COMPROMISE - VSCODE EXTENSIONS
The Developer Environment as Crown Jewel
VSCode marketplace extensions represent a unique attack surface directly compromising the foundation of all software development. Compromising developers and you compromise all the software they produce.
Scale of Attack:
- 1.5 million developers directly affected
- ChatGPT Chinese edition: 1.34 million installations
- ChatMoss: 150,000 installations
- Fortune 500 exposure: ~2,000 major enterprise developers compromised
- Open-source impact: Tens of thousands of GitHub projects
What Developers Have Access To
Each developer's workspace contains organizational crown jewels:
- Complete source code repositories (proprietary algorithms)
- Cloud credentials (AWS keys, Azure tokens, GCP keys)
- Database connection strings (direct database access)
- API tokens (third-party service authentication)
- Private encryption keys (full security bypass)
- Customer data (embedded in code/configurations)
- Unreleased product plans (competitive intelligence)
- Employee credentials (lateral movement vectors)
Developer compromise = organizational compromise. With 1.5 million developers compromised:
- 1+ billion lines of code accessible
- 500+ million cloud credentials available
- 100+ million API keys exposed
- 30+ million database connection strings compromised
MaliciousCorgi Technical Architecture
Attack Mechanism #1: Real-Time File Surveillance
Malicious extensions monitored every file opened and every keystroke:
- Every file opened → content sent to attacker
- Every character typed → incremental changes sent
- Real-time transmission to China-based servers (aihao123.cn)
- Base64 encoding to evade detection
Attack Mechanism #2: Server-Controlled Bulk Harvesting
Extensions received commands from attacker servers to extract specific files:
- Command: Extract 50 files matching the pattern
- Attacker specifies patterns:
**/*.env,secrets/**,config/** - Server-side control enables adaptive targeting
- Attackers harvest the highest-value files first
Attack Mechanism #3: Invisible Profiling
Hidden analytics profiled developers across four tracking platforms:
- Zhuge.io (behavior tracking)
- GrowingIO (event analytics)
- TalkingData (demographic profiling)
- Baidu Analytics (identity correlation)
Combined Effect: Extensions created developer identity profiles linked to:
- Organization affiliation
- Project involvement
- Security clearance level (inferred)
- Contractor status (government projects)
- Development practices (security maturity assessment)
Supply Chain Exponential Risk
If compromised developers push malicious code to open-source projects:
Single npm package compromise
→ 50,000 direct dependents infected
→ 5 million indirect dependents compromised
→ 250 million end-users using backdoored code
→ AWS, Google, Microsoft, Fortune 500 applications affected
Real Recent Example: September 2025 npm attack compromised 180+ packages when a single maintainer account was compromised. The attack lasted 2 hours but achieved:
- Billions of package downloads
- Automatic CI/CD installations
- Cryptocurrency wallet drains
- Transaction interception
Estimated Data Exfiltration
Over 90 days with 1.5 million installations (assuming 50% active use = 750,000 developers):
| Data Category | Volume | Sensitivity |
|---|---|---|
| Source code | 50-500 MB per developer | CRITICAL |
| Cloud credentials | 10-100 per developer | CRITICAL |
| API keys | 20-200 per developer | CRITICAL |
| Database passwords | 5-20 per developer | CRITICAL |
| Private encryption keys | 1-10 per developer | CRITICAL |
| Potential total | 15+ petabytes | CATASTROPHIC |
PART IV: EMAIL INFRASTRUCTURE COMPROMISE - SMARTERMAIL AUTH BYPASS
Email Systems as Organizational Lifeline
Email systems contain the complete organizational intelligence:
- All business communications (strategic decisions, M&A plans, contracts)
- Credential stores (password resets, MFA codes, OAuth tokens)
- Identity verification mechanisms (email as 2FA factor)
- Compliance records (legal evidence, regulatory documentation)
- Customer data (PII, financial information, health records)
Email compromise creates cascading damage:
- Real-time communication monitoring
- Credential harvesting from reset emails
- 2FA code interception for other systems
- Business email compromise (BEC) fraud
- Cloud system access via email (Office 365, Salesforce, Box)
- Ransomware deployment foundation
SmarterMail CVE-2026-23760 Technical Details
Stage 1: Unauthenticated Password Reset
The /api/v1/auth/force-reset-password endpoint lacks authentication checking:
- Attacker sends an HTTP POST without credentials
- Server processes requests as if authorized
- Any user password can be reset (including admins)
IsSysAdminflag elevated to true
Stage 2: OS Command Execution
Once authenticated as admin:
- Navigate to Settings → Storage → Add Volume Mount
- Enter the OS command in the "Volume Mount Command" field
- SmarterMail executes with SYSTEM privileges
- Full server compromise achieved
Combined Impact: Two-stage attack transforms a simple HTTP request into a complete server takeover.
Exploitation Timeline
Observed Progression:
- January 22, 2026: Vulnerability disclosed, patch released
- January 24, 2026: Mass exploitation begins (2 days post-patch)
- January 24-25, 2026: Attackers reverse-engineer patch
- January 26, 2026: Active exploitation ongoing across 1000+ organizations
Why So Fast:
Attackers use patch reverse-engineering:
- Compare patched vs. unpatched code
- Identify changed code (the vulnerability)
- Understand the exploitation method
- Craft exploit in hours
Organizational Risk Assessment
| Organization Type | Email Criticality | Compromise Impact | Estimated Loss |
|---|---|---|---|
| Enterprise (1000+) | CRITICAL | Complete network compromise | $10-100M |
| Financial/Healthcare | CRITICAL | Regulatory fines (4-20% revenue) | $50-500M |
| Government | CRITICAL | National security breach | $100M-1B+ |
| Small business | CRITICAL | Business closure likely | $1-10M |
PART V: MULTI-VECTOR ATTACK CONVERGENCE
The Coordinated Attack Scenario
Sophisticated nation-state or organized crime groups would not attack these systems independently. Instead, they coordinate:
Week 1: Preparation
- VSCode malicious extension campaign begins
- Target Fortune 500 developers in critical sectors
- Harvest AWS/database credentials from .env files
Week 2: Developer Compromise
- Compromised developers' credentials captured
- Attacker gains cloud infrastructure access
- Creates persistence in CI/CD pipelines
- Builds an internal network map from stolen credentials
Week 3: Email Infrastructure Takeover
- Exploit SmarterMail CVE-2026-23760
- Create backdoor admin accounts
- Set up email forwarding to the attacker infrastructure
- Harvest credentials from password reset emails
Week 4: Communications Disruption
- Exploit Cisco UCM CVE-2026-20045 with stolen credentials
- Compromise emergency services 911 center UCM
- Disable communications during ransomware deployment
- Maximize ransom negotiation pressure
Week 5: Total System Compromise
- Ransomware deployed across the organization
- All communications monitored (email + phone)
- Source code backdoored (developer compromise)
- Cloud infrastructure controlled (credential theft)
- Business is completely paralyzed
- Ransom demand: $50-200M
Why This Convergence Is New
Historically: These attacks were compartmentalized
- Ransomware groups focused on RCE
- Credential theft was secondary
- Supply chain attacks targeted specific industries
- Email compromise was isolated
2026 Reality: Adversaries systematically chain vulnerabilities because:
- AI acceleration enables rapid exploitation
- Vulnerability acceleration provides attack options
- Supply chain attacks are now normalized
- Nation-state investment enables multi-vector operations
PART VI: ORGANIZATIONAL RESPONSE FRAMEWORK
Immediate Actions (Days 1-7)
Cisco UCM Users:
- Identify all deployments (internet-exposed and internal)
- Apply patches for CVE-2026-20045 immediately
- Isolate UCM from internet via firewall rules
- Implement network segmentation (UCM on separate VLAN)
- Monitor for exploitation indicators
- Audit all accounts for unauthorized access
SmarterMail Users:
- Upgrade to version 9511+ immediately
- Audit all admin accounts
- Delete suspicious email forwarding rules
- Reset all passwords after patching
- Monitor logs for suspicious volume mount commands
- Review recent admin actions in audit logs
VSCode Users:
- Audit all installed extensions
- Uninstall ChatGPT Chinese, ChatMoss, similar extensions
- Rotate ALL AWS/database credentials immediately
- Audit Git commit history for malicious code
- Review CI/CD logs for unauthorized deployments
- Scan developer machines for persistence mechanisms
Medium-Term Hardening (Weeks 2-4)
Zero Trust Architecture:
- Identity-based access controls
- MFA for all systems (hardware tokens preferred)
- Network segmentation by function
- Continuous verification (re-auth every 12 hours)
- Behavioral analytics (UEBA) for anomaly detection
Credential Management:
- Vault solution deployment (Hashicorp Vault, AWS Secrets Manager)
- Eliminate hardcoded credentials
- Audit developers' machines for stored credentials
- Secret scanning in CI/CD pipelines
- Enforce short-lived credentials (15min-1hr TTL)
Supply Chain Security:
- SBOM (Software Bill of Materials) for all dependencies
- Dependency scanning in build pipelines
- Pin dependency versions (avoid auto-updates)
- Code review for new packages
- Network isolation for package managers
Strategic Initiatives (Months 2-6)
Infrastructure Modernization:
- Replace legacy systems (5+ year-old systems)
- Modern authentication (OIDC/SAML, not basic auth)
- Cloud-native deployment models
- Automated patching infrastructure
Detection & Response:
- SOC maturity assessment
- Threat detection rule development
- Incident response playbooks
- Threat hunting program
- Tabletop exercises
Governance:
- Software supply chain risk management program
- Vendor security assessment
- SBOM requirements
- Secure development lifecycle training
- Third-party risk management
PART VII: THREAT INTELLIGENCE & FUTURE PROJECTIONS
Vulnerability Acceleration Trajectory
| Year | Zero-Days | Growth Rate | Driving Factors |
|---|---|---|---|
| 2024 | 90 | Baseline | Traditional research |
| 2025 | 200-250 | 180% | AI-assisted fuzzing beginning |
| 2026 | 400-500 | 100% | Nation-state investment peak |
Drivers: AI-assisted vulnerability discovery, exploit automation, commercial zero-day markets ($5-10M per critical vulnerability), nation-state investment
Attack Speed Reduction Timeline
| Metric | 2022 | 2025 | 2026 Projection |
|---|---|---|---|
| Discovery to PoC | 30 days | 5 days | 1 day |
| PoC to mass exploitation | 15 days | 2 days | Hours |
| Patch to bypass | 7 days | Hours | Minutes |
| Breach to persistence | Days | Hours | Minutes |
Critical Implication: Organizations have effectively zero time to respond after disclosure. Defense must shift from reactive patching to proactive containment.
Emerging Attack Vectors (Next 12 Months)
AI Integration Attacks:
- Prompt injection against LLM-based security tools
- Training data poisoning
- Model extraction attacks
OT/ICS Convergence:
- 2,451 ICS vulnerabilities disclosed Dec 2024-Nov 2025
- Pro-Russian hacktivists targeting infrastructure
- Ransomware hitting critical infrastructure (355% increase since 2020)
Identity Compromise:
- Zero-day attacks on identity systems (Azure AD, Okta)
- Authentication bypass is becoming the primary vector
- OAuth/SAML exploitation is increasing
CONCLUSION: THE NEW SECURITY IMPERATIVE
The January 2026 threat convergence represents a fundamental shift in cybersecurity risk:
Legacy Assumption: Organizations have time to patch; layered defenses prevent total compromise
2026 Reality: Organizations must assume exploitation is occurring; containment is primary defense
Critical Insight: These three threats are not aberrations—they represent the new baseline for threat sophistication, speed, and scale.
Organizations must shift from:
- Patch-driven security → Containment-driven security
- Perimeter defense → Zero-trust architecture
- Reactive response → Proactive threat hunting
- Patching as primary defense → Segmentation + behavioral detection
The organizations surviving 2026 won't be those that patch fastest. There will be those that assume compromise and contain damage automatically before humans know intrusions are occurring.
Report Date: January 26, 2026
Enjoyed this article?
Subscribe for more cybersecurity insights.
