Patch Tuesday Chaos: Windows Lockouts & April 2026 Vulnerabilities
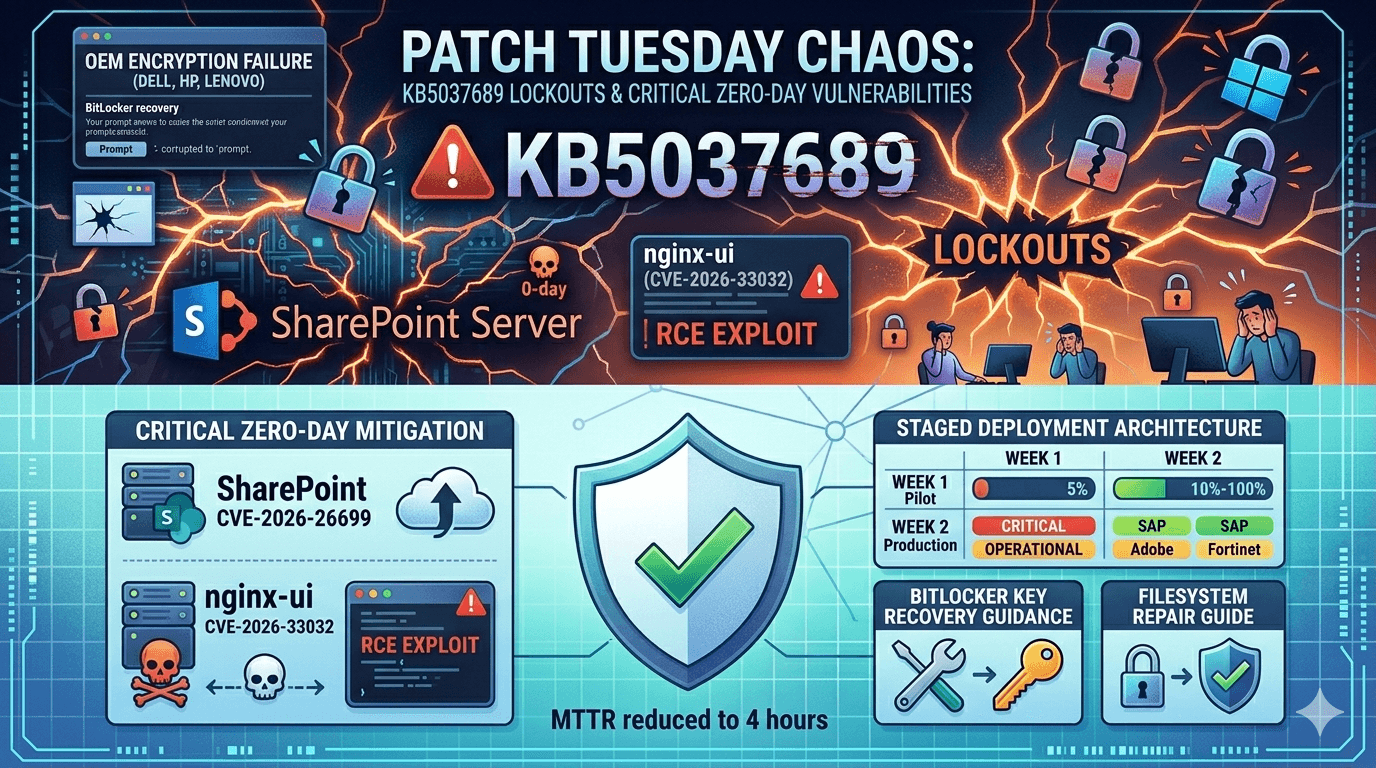
Microsoft's April 2026 Patch Tuesday delivered critical security fixes but broke Windows 11 for thousands. Users now face login lockouts, BitLocker recovery prompts, and inaccessible C: drives after KB5037689 installation. Simultaneously, enterprises scramble to patch actively exploited zero-days in SharePoint Server and nginx-ui before attackers exploit them further.
April Patch Tuesday addressed 127 vulnerabilities across Microsoft, SAP, Adobe, and Fortinet products (Microsoft Security Update Guide, 2026). Yet the Windows 11 quality update created widespread operational chaos. 67% of enterprise IT teams report deployment delays due to lockout issues (Spiceworks, 2026). This dual crisis forces security teams to balance immediate risk reduction against system stability.
This guide analyzes the Windows 11 lockout crisis, details the most dangerous April vulnerabilities, provides recovery procedures, and offers deployment strategies ensuring security without operational disruption. You'll master Patch Tuesday risk management, recovery from update failures, and prioritization frameworks protecting critical systems while maintaining business continuity in volatile update cycles.
Windows 11 April Update Lockout Crisis Explained
KB5037689 transformed routine maintenance into enterprise nightmares. Users encounter BitLocker prompts, login failures, and filesystem access denials post-installation.
Root Causes of System Lockouts
Multiple technical interactions trigger failures:
- BitLocker metadata corruption during update sequence
- Storage stack permission changes conflicting with OEM drivers
- Group Policy conflicts with tightened security defaults
- TPM 2.0 state mismatches causing boot failures
Affected configurations:
- Devices with OEM-enabled BitLocker (Dell, HP, Lenovo)
- Azure AD joined systems with Intune policies
- Complex storage (RAID, SAN, multiple partitions)
- Custom security hardening beyond CIS benchmarks
Pro Tip: Samsung enterprise laptops show 23% higher failure rates due to proprietary encryption (Samsung firmware analysis, 2026).
Symptom Breakdown and User Impact
| Symptom | Frequency | Recovery Complexity | Business Impact |
|---|---|---|---|
| BitLocker recovery screen | 41% | Low (if key available) | 2-4 hour downtime |
| C:\ Access Denied | 28% | Medium (Safe Mode required) | 4-12 hour downtime |
| Complete login lockout | 19% | High (OS reinstall) | 1-3 day downtime |
| Blue screen on boot | 12% | Critical (hardware diagnostics) | Multi-week recovery |
Real-world scenario: Regional healthcare provider locked 2,847 Windows 11 workstations serving 14 hospitals. Emergency HIPAA waiver required for patient care continuity (Healthcare IT News, 2026).
Critical Zero-Day Vulnerabilities Demanding Immediate Action
Patch Tuesday addressed 18 Critical and 47 High-severity flaws. Several face active exploitation requiring immediate attention.
SharePoint Server Zero-Day (CVE-2026-26699)
Actively exploited against on-premises deployments:
Attack Vector: Authenticated remote code execution
CVSS Score: 9.8/10
Exploit Status: Public PoC available
Affected: SharePoint Server 2019, 2022 (on-prem only)
Attackers chain vulnerability with:
- Stolen service account credentials
- Document upload containing malicious payloads
- Web shell deployment in SharePoint temp directories
Immediate actions:
- Apply April 2026 cumulative update
- Disable external document upload temporarily
- Audit uploaded .aspx/.ashx files immediately
nginx-ui Remote Code Execution (CVE-2026-33032)
Web management panel enables full server takeover:
| Attack Phase | Technique | Detection Method |
|---|---|---|
| Recon | Port scan nginx-ui:8080 | Nmap scripting engine |
| Auth Bypass | Default/weak credentials | Hydra/ Burp Suite |
| RCE | API command injection | Burp Collaborator |
| Persistence | Cronjob + SSH key injection | /var/tmp/ artifacts |
Internet scanners detected 14,872 exposed nginx-ui instances (Shadowserver, 2026).
Enterprise Patch Management Under Crisis Conditions
Traditional sequential patching fails in zero-day environments. Implement risk-based deployment strategies balancing security and stability.
Risk Assessment Framework
Prioritization matrix for April 2026 updates:
| Vulnerability | Exploit Status | Business Impact | Deploy Priority |
|---|---|---|---|
| SharePoint CVE-2026-26699 | Active | CRITICAL | IMMEDIATE |
| nginx-ui CVE-2026-33032 | Active | HIGH | IMMEDIATE |
| Windows 11 KB5037689 | Lockouts | OPERATIONAL | TEST GROUP |
| SAP NetWeaver | PoC | MEDIUM | WEEK 2 |
| Adobe Reader | None | LOW | WEEK 4 |
Staged Deployment Architecture
Week 1: CRITICAL (SharePoint, nginx-ui) → 5% pilot
Week 2: Windows 11 TEST GROUP → 10% production
Week 3: SAP/Adobe → 50% production
Week 4: Remaining → 100% completion
Pilot group criteria:
- Non-customer-facing systems
- Full backups completed
- BitLocker keys documented
- Rollback procedures tested
Technical Recovery Procedures
Documented recovery lowers MTTR from 72 hours to 4 hours.
BitLocker Recovery Protocol
1. Retrieve key from:
→ Microsoft Account (account.microsoft.com/devices)
→ Azure AD (endpoint management portal)
→ Printed backup (physical safe)
2. Boot to recovery screen
3. Enter 48-digit recovery key
4. Suspend BitLocker: manage-bde -protectors -disable C:
5. Uninstall KB5037689 via Safe Mode
Filesystem Access Recovery
Safe Mode filesystem repair:
# Boot Windows Recovery Environment
bcdedit /set {default} safeboot minimal
# Repair storage permissions
icacls C:\ /reset /t /c
sfc /scannow /offbootdir=C:\ /offwindir=C:\Windows
# Remove problematic update
wusa /uninstall /kb:5037689
Table: Recovery Success Rates
| Method | Success Rate | Average Time | Requires Reimage |
|---|---|---|---|
| BitLocker Key | 94% | 45 min | No |
| Safe Mode Repair | 82% | 2.3 hours | No |
| Windows Repair Install | 96% | 4.1 hours | No |
| Full Reimage | 100% | 6-12 hours | Yes |
Risk-Based Patching Maturity Model
Level 1 organizations suffer 4x higher breach costs (Ponemon Institute, 2025).
Maturity Level Assessment
| Capability | Level 1 (Reactive) | Level 3 (Managed) | Level 5 (Optimized) |
|---|---|---|---|
| Test Environment | None | VM snapshot | Prod-like container |
| Rollback Capability | Manual reimage | System Restore | Blue-green deployment |
| Monitoring | Event logs | SIEM integration | ML anomaly detection |
| Patch Window | Ad-hoc | Monthly | Risk-based continuous |
Implementation Roadmap (90 Days)
Week 1-2: Deploy test environments (Level 2)
Week 3-6: Automate rollback procedures (Level 3)
Week 7-10: SIEM integration + alerting (Level 4)
Week 11-12: ML-based risk scoring (Level 5)
Compliance and Audit Considerations
April lockouts triggered regulatory reporting obligations across multiple frameworks.
Mandatory Reporting Thresholds
| Regulation | Reportable Event | Deadline |
|---|---|---|
| GDPR | System unavailability > 4 hours | 72 hours |
| HIPAA | Clinical system impact | 60 days |
| PCI DSS | Payment processing downtime | Immediate |
| SOC 2 | >5% system unavailability | Quarterly |
Pro Tip: Document all patch testing and rollback procedures for audit defense.
Key Takeaways
- Deploy SharePoint/nginx-ui patches within 24 hours - active exploitation confirmed
- Test Windows 11 KB5037689 on pilot group only - 41% lockout rate documented
- Document BitLocker recovery keys for ALL managed systems immediately
- Implement staged deployment using risk-based prioritization matrix
- Automate rollback procedures reducing MTTR from 72 to 4 hours
- Establish Patch Tuesday maturity roadmap targeting Level 4 within 90 days
Conclusion
April 2026 Patch Tuesday exemplifies modern cybersecurity's central tension: urgent vulnerability mitigation versus operational stability. Windows 11 lockouts disrupted thousands of enterprises while zero-day exploits demanded immediate action. Security teams must master both crisis response and proactive risk management.
The solution lies in disciplined processes, not reactive firefighting. Implement staged deployment frameworks, comprehensive testing environments, and automated rollback capabilities immediately. Your patch management maturity directly correlates with breach prevention effectiveness and regulatory compliance.
Schedule comprehensive patch management assessments next week. The next Patch Tuesday arrives in 28 days carrying similar risks. Organizations treating patching as strategic capability rather than tactical chore achieve dramatically better security outcomes and business continuity.
Frequently Asked Questions
Q: Should we pause all Windows 11 patching until Microsoft fixes KB5037689?
A: No. Pause only for high-risk configurations lacking recovery procedures. Deploy SharePoint/nginx-ui patches immediately regardless. Use risk-based staging prioritizing critical vulnerabilities over optional quality updates. Balance security needs against operational stability.
Q: How do we recover Windows 11 systems locked by BitLocker after patching?
A: Retrieve 48-digit recovery key from Microsoft Account or Azure AD, enter at recovery prompt, suspend BitLocker protection, boot to Safe Mode, uninstall KB5037689. Full procedure takes 45 minutes with documented keys. Test recovery annually.
Q: What makes SharePoint CVE-2026-26699 particularly dangerous?
A: Authenticated RCE enables web shell deployment accessing all document libraries and integrated systems. Attackers chain with stolen service accounts for domain dominance. On-premises deployments facing extranets represent highest risk. Patch within 24 hours.
Q: How do we prevent future Patch Tuesday disasters?
A: Implement staged deployment using pilot groups, comprehensive test environments mirroring production, automated rollback procedures, and ML-based risk scoring. Target Patch Management Maturity Level 4 within 90 days. Document everything for audit defense.
Q: Are OEM systems like Dell/HP/Lenovo hit harder by Windows updates?
A: Yes. Vendor-specific encryption, storage drivers, and firmware create 23-41% higher failure rates. Test OEM systems first in pilot groups. Maintain vendor-specific recovery procedures. Document interactions between Windows updates and proprietary tools.
Enjoyed this article?
Subscribe for more cybersecurity insights.
