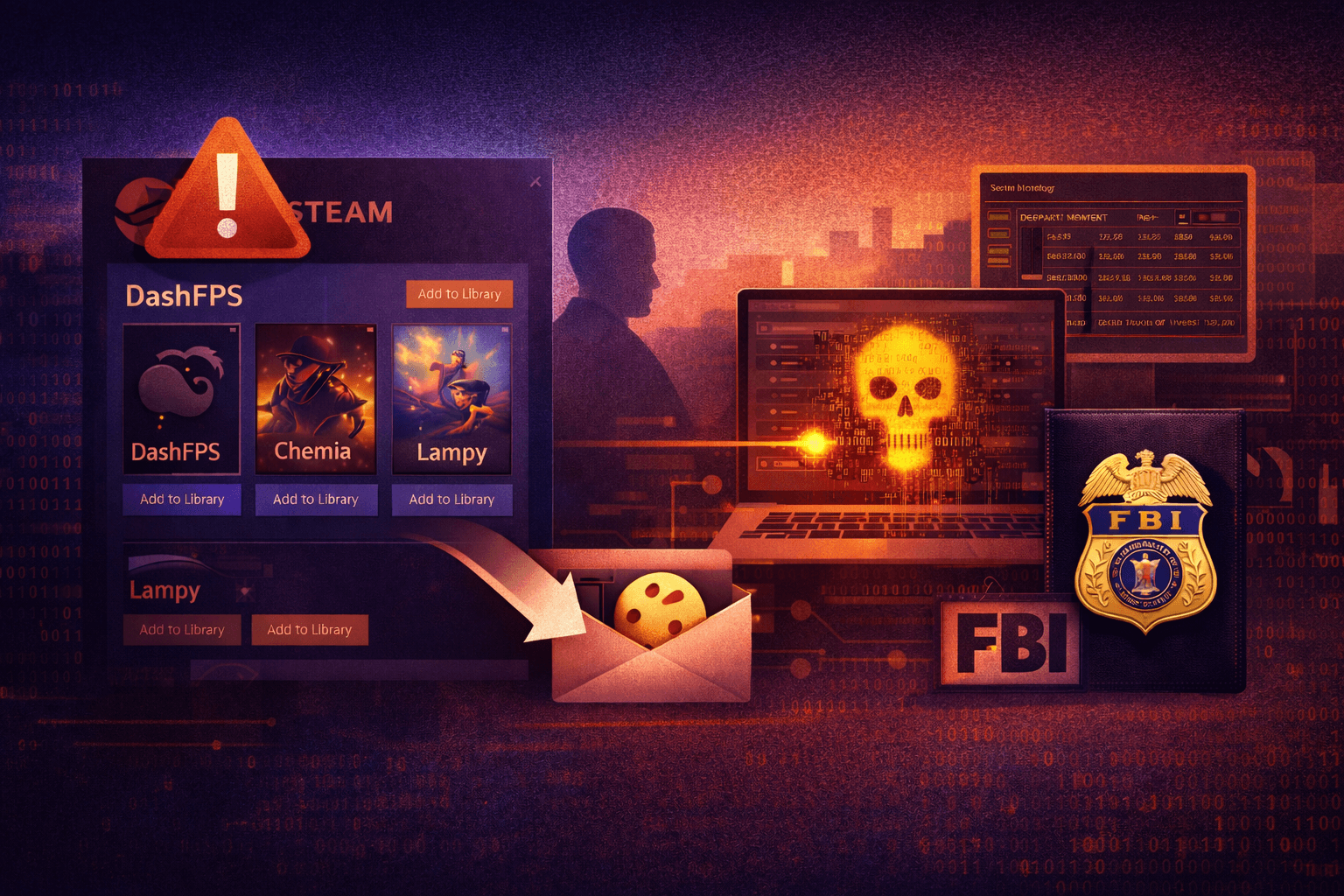
A federal investigation is exposing a threat that most organizations never see coming: malware distributed through one of the world's most trusted gaming platforms. The FBI's Seattle Division is actively investigating a threat actor who allegedly published at least seven games on Steam between May 2024 and January 2026, each designed to install information-stealing malware on players' machines. The named titles — BlockBlasters, Chemia, Dashverse/DashFPS, Lampy, Lunara, PirateFi, and Tokenova — were all attributed to the same actor and made available through Steam's standard publishing pipeline.
This case matters far beyond the gaming community. Corporate employees, developers, and IT staff play games on personal and work-adjacent devices. Session cookies, saved credentials, and authentication tokens don't distinguish between a gaming session and a business one. If your organization allows personal devices in any capacity, or if your employees use shared machines, this attack vector reaches directly into your environment. This article explains how the campaign worked, what data was at risk, and what defenders can do right now.
How Malicious Games Bypassed Steam's Publishing Pipeline
Steam is the dominant PC gaming distribution platform, with over 130 million active users (industry estimate, 2024). Its scale and reputation create an implicit trust problem: users and security tools alike tend to treat software distributed through established storefronts as inherently safer than software downloaded from unknown sources. This campaign exploited that assumption directly.
The Publishing Pipeline as an Attack Vector
Valve's Steam platform allows independent developers to publish games through a self-service submission process. While Valve conducts reviews, the volume of submissions — thousands of titles per year — makes deep behavioral analysis of every executable impractical. The alleged threat actor took advantage of this gap by packaging functional or near-functional game experiences around malicious payloads, creating enough surface legitimacy to pass initial review and attract real users.
This is a software supply chain attack applied to a consumer distribution channel. The threat model mirrors enterprise supply chain compromises — an attacker inserts malicious code into a trusted distribution mechanism — but targets consumer endpoints that may have access to corporate resources.
What the Malware Actually Did
According to the FBI's investigation, the games installed information-stealing malware capable of:
- Harvesting session cookies from browsers, granting attackers access to authenticated web sessions
- Exfiltrating saved passwords and autofill credentials stored in browsers
- Capturing system and environment information useful for further targeting
- Potentially stealing cryptocurrency wallet data and exchange session tokens
The session cookie theft component is particularly damaging. A valid session cookie allows an attacker to impersonate an authenticated user without knowing their password or triggering a multi-factor authentication (MFA) challenge. This technique, known as pass-the-cookie or session hijacking, effectively nullifies standard 2FA protections on any service the victim was logged into.
Table: Malware Capability Impact by Target Data Type
| Data Type Stolen | Attack Capability Enabled | MFA Bypassed? | Severity |
|---|---|---|---|
| Session cookies | Account takeover without password | Yes | Critical |
| Saved passwords | Direct credential replay | Partial | High |
| Crypto wallet data | Asset theft | N/A | Critical |
| System fingerprint | Targeted follow-on attack | N/A | Medium |
| Browser history | Phishing personalization | N/A | Low–Medium |
The Broader Risk: Gaming Platforms as Enterprise Threat Vectors
How does a compromised Steam account become a corporate security incident? The answer lies in how modern work and personal computing overlap — and how information stealers don't limit their collection to gaming-related data.
Credential and Session Spillover
Most users log into dozens of services through the same browser profile. A session cookie harvested from a personal gaming session may include active tokens for:
- Corporate SSO (Single Sign-On) portals and VPN authentication flows
- SaaS platforms like email, project management tools, and cloud storage
- Code repositories accessed through browser-based interfaces
- Cloud console sessions for AWS, Azure, or GCP
Important: Many organizations enforce MFA on initial login but issue long-lived session tokens that persist for hours or days. An attacker with a valid session cookie does not need to re-authenticate and will not trigger MFA challenges during that session window.
The BYOD and Personal Device Risk
Bring Your Own Device (BYOD) policies, remote work arrangements, and the use of personal machines for after-hours work create direct pathways from a compromised gaming session to enterprise resources. Even organizations with strict endpoint management policies face exposure if employees access corporate email or VPN through personal browsers on unmanaged devices.
Table: Exposure Risk by Device and Policy Type
| Device Type | Policy | Corporate Data Exposure Risk | Primary Concern |
|---|---|---|---|
| Managed corporate laptop | Full MDM + EDR | Low | Lateral movement post-infection |
| Personal device, BYOD enrolled | Partial MDM | Medium–High | Uncontrolled browser sessions |
| Personal device, no enrollment | None | High | Full credential/cookie exposure |
| Shared home/family computer | None | Very High | Multiple users, no isolation |
| Corporate device used for gaming | Full MDM + EDR | Medium | Policy violation + malware risk |
Incident Response and the FBI's Victim Portal
The FBI's decision to publish a victim-information portal marks an important and relatively uncommon step in the law enforcement response to cybercrime. The portal asks affected users to submit information about their experience, supporting both the ongoing federal prosecution and potential restitution for victims.
What Affected Users Should Do
If you or anyone in your organization downloaded any of the named titles — BlockBlasters, Chemia, Dashverse/DashFPS, Lampy, Lunara, PirateFi, or Tokenova — treat the affected machine as compromised and take immediate action:
- Isolate the device from corporate networks and shared resources
- Revoke all active browser sessions across every service the device accessed — log out everywhere, not just on the affected machine
- Rotate credentials for every account the victim used on that device, prioritizing corporate SSO, email, and financial services
- Invalidate API tokens and OAuth grants associated with the affected account
- Submit information to the FBI portal to support the federal case and establish victim status for potential restitution
- Preserve forensic artifacts — browser history, installed application logs, and network connection records — before wiping the device
- Run a full malware scan using updated definitions, but do not rely solely on this; reimage the machine if corporate data was accessible
Coordinating with Law Enforcement
This case is a useful model for understanding how to engage with federal investigators when an incident involves active criminal prosecution. The FBI's victim portal lowers the barrier to reporting significantly. Organizations whose employees were affected should consider whether reporting through corporate counsel aligns with their incident response (IR) plan — participation may support restitution and contributes to the broader case against the threat actor.
Pro Tip: Update your IR playbooks now to include a step for checking active FBI and CISA advisories when the infection vector involves a third-party platform or supply chain component. Federal investigations sometimes surface IOCs (Indicators of Compromise) before they appear in commercial threat feeds.
Defensive Controls: Treating Distribution Channels as Untrusted
This campaign forces a hard conversation about implicit trust in software distribution. "Downloaded from a reputable store" has never been a security control — it is a convenience assumption. Your defenses need to reflect that reality.
Endpoint and Application Controls
- Enforce application allowlisting on managed devices using CIS Control 2 (Inventory and Control of Software Assets) — only pre-approved executables run, regardless of their distribution source
- Deploy behavioral EDR (Endpoint Detection and Response) that flags credential harvesting behaviors, browser process injection, and abnormal cookie access patterns at runtime
- Restrict browser credential storage via group policy or MDM — prevent browsers from saving passwords on corporate or BYOD-enrolled devices
- Separate browser profiles for work and personal use, with work profiles sandboxed or limited to managed browsers
Session and Identity Hardening
- Implement short session token lifetimes for all corporate SSO and SaaS platforms — reduce the window during which a stolen cookie remains valid
- Enable device-bound session tokens where supported (Google's Device Bound Session Credentials, Microsoft's Continuous Access Evaluation) so tokens cannot be replayed from unfamiliar devices
- Deploy impossible travel and anomalous session detection in your identity provider to flag session reuse from unexpected geolocations or device fingerprints
- Enforce FIDO2/passkey authentication for privileged accounts — these credentials are device-bound and cannot be stolen by cookie harvesters
Table: Defensive Control Effectiveness Against Info-Stealer Campaigns
| Control | Prevents Initial Infection | Limits Data Exfiltration | Detects Post-Infection Activity |
|---|---|---|---|
| Application allowlisting | Yes (if enforced) | N/A | N/A |
| Behavioral EDR | Partial | Partial | Yes |
| Short session token TTL | No | No | N/A — limits impact |
| Device-bound session tokens | No | No | N/A — blocks replay |
| FIDO2 / passkeys | No | No | N/A — blocks ATO |
| Browser credential restriction | No | Yes | No |
| Anomalous session detection | No | No | Yes |
Key Takeaways
- Revoke sessions immediately if any device in your environment ran a named title — session cookie theft enables account takeover without triggering MFA, making rapid revocation the most critical first step
- Treat consumer distribution platforms as untrusted sources — application store provenance is not a security control; enforce endpoint controls that apply regardless of where software originated
- Update BYOD and personal device policies to explicitly address gaming software and the risk of credential spillover to corporate resources
- Shorten session token lifetimes across corporate SSO and critical SaaS platforms to reduce the window of exploitation for any stolen cookie
- Submit to the FBI victim portal if affected — participation supports federal prosecution and establishes victim status for potential restitution
- Add supply chain checks to your IR playbook — when any third-party distribution channel is the infection vector, cross-reference active law enforcement advisories as a standard step
Conclusion
The Steam malware campaign is a supply chain attack aimed at consumer infrastructure — but its consequences reach directly into enterprise environments through shared devices, BYOD policies, and the session cookies that authenticate your employees to corporate systems. Seven games, one threat actor, and an unknown number of compromised machines represent a tangible, ongoing risk to organizations of every size.
The FBI's active investigation and victim portal create an unusual opportunity: organizations and individuals can contribute directly to a federal prosecution while protecting themselves. Start with the immediate response steps for any affected device, then use this case as the forcing function to review your session token policies, BYOD controls, and endpoint application governance. The gaming industry will not be the last consumer platform weaponized this way — your defenses need to assume that trusted distribution channels can be compromised.
Frequently Asked Questions
Q: Which Steam games contained malware according to the FBI investigation? A: The FBI's Seattle Division named seven titles believed to originate from the same threat actor: BlockBlasters, Chemia, Dashverse/DashFPS, Lampy, Lunara, PirateFi, and Tokenova. If you installed any of these games between May 2024 and January 2026, treat the affected device as compromised and follow the incident response steps outlined above.
Q: How does session cookie theft bypass multi-factor authentication? A: When you authenticate to a web service, the server issues a session cookie that your browser presents on subsequent requests — this is how the site knows you are already logged in. An attacker who steals that cookie can present it from their own browser, inheriting your authenticated session without needing your password or MFA code. The server has no reliable way to distinguish the legitimate session from the replayed one unless device-binding or behavioral anomaly detection is in place.
Q: Should organizations be concerned if employees only played these games on personal devices? A: Yes. Personal devices used for any work-related activity — checking corporate email, connecting to VPN, accessing SaaS tools — share browser sessions across work and personal contexts. A session cookie harvested from a gaming session on a personal device may include valid tokens for corporate resources if the same browser profile was used for both.
Q: How do I report to the FBI if I was affected? A: The FBI's Seattle Division has published a victim-information portal specifically for this investigation. Search for the FBI's official victim assistance portal or visit ic3.gov for guidance on submitting information. Affected organizations should involve legal counsel before submitting to understand how the submission interacts with any parallel regulatory reporting obligations under GDPR, HIPAA, or applicable state breach notification laws.
Q: What is the best long-term control to prevent session hijacking from info-stealers? A: The most effective technical controls are device-bound session tokens — such as Google's Device Bound Session Credentials or Microsoft's Continuous Access Evaluation — combined with FIDO2/passkey authentication for privileged accounts. These mechanisms bind authentication and session validity to a specific device, making stolen cookies non-replayable from an attacker's machine. Short session token lifetimes (under four hours for sensitive applications) provide an important secondary layer that limits the exploitation window even when a cookie is successfully stolen.
Enjoyed this article?
Subscribe for more cybersecurity insights.
