A state-sponsored threat actor silently compromised 53 organizations across 42 countries — and your security tools likely never flagged a single suspicious connection. That is the alarming reality of GRIDTIDE, a sophisticated espionage campaign attributed to UNC2814, a China-nexus threat group recently disrupted through a coordinated effort between Google and Mandiant. The campaign targeted telecommunications providers, government agencies, and internet service providers (ISPs), with a singular focus: covert intelligence collection at global scale.
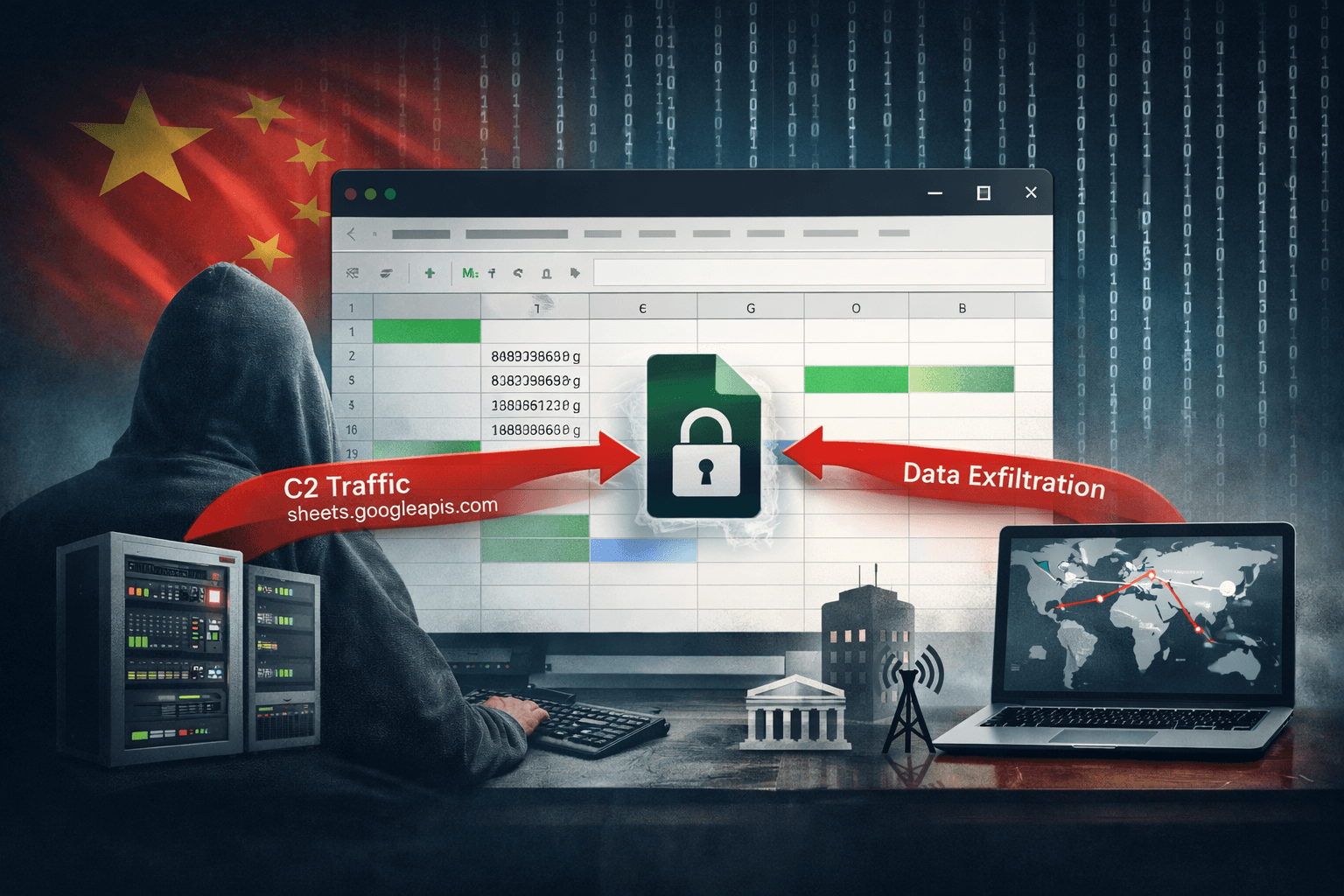
What makes GRIDTIDE particularly dangerous is not just its reach — it is the method. Attackers weaponized Google Sheets, a trusted and ubiquitous cloud productivity tool, as their command-and-control (C2) infrastructure. By hiding instructions inside spreadsheet cells and polling for responses, UNC2814 effectively disguised malicious traffic as legitimate SaaS activity. This guide breaks down how the campaign worked, what it means for defenders, and the concrete steps your security operations center (SOC) should take right now.
How UNC2814 Built a C2 Channel Inside Google Sheets
Understanding the GRIDTIDE campaign starts with understanding its most novel feature: the abuse of the Google Sheets API for stealthy C2 communication. This technique exploits the implicit trust most organizations extend to Google's infrastructure.
The GRIDTIDE Backdoor Mechanics
The GRIDTIDE backdoor, once deployed on a compromised edge device, established outbound connections exclusively to Google's legitimate API endpoints. Operators stored encoded commands inside spreadsheet cells, and the implant polled those cells at regular intervals to retrieve instructions. Exfiltrated data traveled back through the same channel.
This approach eliminated the need for direct attacker-to-victim connections — a hallmark of traditional C2 architectures that most detection tools are built to catch. Key behavioral indicators of the backdoor include:
- Anomalous Google Sheets API calls originating from network edge devices
- High-frequency polling patterns inconsistent with normal user activity
- Encoded or Base64-formatted cell values within monitored spreadsheets
- Outbound HTTPS traffic to
sheets.googleapis.comfrom servers with no business justification
Why SaaS-Based C2 Evades Traditional Defenses
Most perimeter security tools operate on reputation-based blocking. Because googleapis.com carries an inherently trusted reputation, traffic to it rarely triggers alerts. Attackers have recognized this blind spot. The MITRE ATT&CK framework categorizes this technique under T1102 – Web Service and T1567 – Exfiltration Over Web Service, but many organizations have not yet built detection rules covering legitimate cloud platforms as C2 carriers.
Important: If your SOC ruleset does not include behavioral baselines for cloud API usage from infrastructure devices, GRIDTIDE-style campaigns will pass through undetected.
Tactics, Techniques, and Procedures: The Full Attack Chain
The GRIDTIDE campaign did not rely on a single clever trick. UNC2814 combined multiple techniques to achieve persistent, low-noise access across targeted networks — a pattern consistent with advanced persistent threat (APT) operations.
SoftEther VPN for Network Pivoting
After initial compromise, operators deployed SoftEther VPN, an open-source virtual private network tool, to facilitate lateral movement and network pivoting. SoftEther is a legitimate application used by enterprises globally, which makes its presence in an environment difficult to flag as inherently malicious. Threat hunters should treat unexpected SoftEther installations on servers or edge appliances as a high-priority indicator of compromise (IOC).
Living-off-the-Land Persistence
UNC2814 relied heavily on living-off-the-land (LotL) techniques — using built-in system tools and trusted applications rather than custom malware — to maintain persistence while minimizing forensic footprint. This approach complicates detection because the activity blends with legitimate administrative operations.
Table: GRIDTIDE Attack Chain vs. MITRE ATT&CK Mapping
| Attack Phase | Technique | MITRE ATT&CK ID |
|---|---|---|
| Initial Access | Edge device exploitation | T1190 |
| Persistence | LotL binaries, scheduled tasks | T1053 |
| C2 Communication | Google Sheets API polling | T1102 |
| Lateral Movement | SoftEther VPN pivoting | T1572 |
| Exfiltration | Data via web service | T1567 |
Target Selection and Espionage Objectives
UNC2814 targeted organizations operating critical communications infrastructure: telecommunications carriers, ISPs, and government ministries. While Mandiant confirmed no definitive data theft at the time of disruption, the campaign's focus on personally identifiable information (PII) collection strongly suggests intelligence-gathering objectives aligned with nation-state espionage priorities. The 53 confirmed breaches across 42 countries indicate a deliberate, globally-scoped operation rather than opportunistic compromise.
Detection Strategies for SOC Teams
The GRIDTIDE campaign demands a fundamental update to how defenders monitor cloud service usage within their environments. Reactive, signature-based detection is insufficient against this class of threat.
Monitoring Cloud API Anomalies
Your detection engineering team should immediately prioritize rules that identify atypical Google API usage patterns from non-user devices. Effective detection queries should flag:
sheets.googleapis.comconnections from servers, routers, or firewall appliances- API call frequency exceeding normal user thresholds (e.g., polling every 30–60 seconds)
- OAuth token usage associated with service accounts accessing spreadsheets containing encoded data
- Unexpected spikes in outbound HTTPS volume to Google infrastructure from OT or network edge segments
Hunting for SoftEther and Lateral Movement Indicators
Threat hunters investigating potential GRIDTIDE exposure should execute targeted hunts across endpoint and network telemetry. Priority hunt queries include searching for SoftEther VPN process execution, unusual VPN tunnel establishment on non-standard ports, and credential access events following edge device compromise.
Pro Tip: Cross-reference any SoftEther detections with concurrent anomalous Google API traffic. The co-occurrence of both signals dramatically increases confidence in a GRIDTIDE-related intrusion.
Table: Detection Priorities by Security Control Layer
| Control Layer | Detection Focus | Priority |
|---|---|---|
| Network | Sheets API from infrastructure devices | Critical |
| Endpoint | SoftEther VPN process execution | High |
| Identity | Anomalous OAuth token activity | High |
| Cloud | Unusual spreadsheet access patterns | Medium |
| Perimeter | Non-standard VPN tunnel ports | Medium |
Disruption, Response, and What Comes Next
Google and Mandiant disrupted the GRIDTIDE campaign through a combination of sinkholing — redirecting C2 traffic to researcher-controlled infrastructure — and the publication of detailed threat intelligence advisories containing TTPs and IOCs. This coordinated disclosure follows an established model for neutralizing APT infrastructure while enabling the broader defender community to respond.
What Sinkholing Achieved
Sinkholing effectively severed UNC2814's ability to issue new commands or retrieve exfiltrated data through the compromised spreadsheet infrastructure. However, defenders should assume that threat actors of this sophistication maintain redundant C2 channels. Organizations in targeted sectors should treat published IOCs as a starting point, not a complete remediation checklist.
Compliance and Regulatory Implications
Organizations subject to GDPR, HIPAA, or NIS2 Directive requirements face notification obligations if GRIDTIDE-related compromise resulted in unauthorized access to regulated data. Even absent confirmed exfiltration, the presence of a backdoor capable of PII collection may trigger breach assessment requirements under Article 33 of GDPR. Legal and compliance teams should initiate impact assessments in parallel with technical response efforts.
Key Takeaways
- Immediately audit your environment for anomalous Google Sheets API traffic originating from network infrastructure and edge devices
- Build MITRE ATT&CK T1102 and T1567 detection rules tailored to cloud productivity platforms as potential C2 carriers
- Hunt proactively for SoftEther VPN installations on any device that does not have a documented business justification
- Treat co-occurrence of SoftEther activity and unusual Google API polling as a high-confidence GRIDTIDE indicator
- Review OAuth token grants and service account permissions for any spreadsheet access that does not align with business operations
- Initiate GDPR or applicable regulatory breach assessments if your organization operates in a targeted sector and cannot rule out compromise
Conclusion
The GRIDTIDE campaign represents a significant evolution in nation-state espionage tradecraft. UNC2814 demonstrated that trusted SaaS platforms like Google Sheets can be transformed into covert command-and-control infrastructure — evading defenses that were never designed to treat legitimate cloud services as threats. The 53 breaches across 42 countries signal that critical infrastructure defenders globally must rethink their detection assumptions.
The disruption by Google and Mandiant provides a critical window of opportunity. Prioritize cloud API behavioral monitoring, update your SOC rulesets to include T1102 and T1567 coverage, and validate that your threat hunting workflows account for living-off-the-land persistence techniques. Review the full Mandiant GRIDTIDE report for the complete IOC list and begin your internal hunt today.
Frequently Asked Questions
Q: What is the GRIDTIDE campaign? GRIDTIDE is a China-linked cyber espionage campaign attributed to threat group UNC2814 that compromised 53 organizations across 42 countries. The campaign is notable for abusing the Google Sheets API as a covert command-and-control channel to evade detection.
Q: How did attackers use Google Sheets for C2 communication? The GRIDTIDE backdoor polled Google Sheets spreadsheet cells at regular intervals to retrieve encoded operator commands and return exfiltrated data. Because the traffic appeared as legitimate Google API calls, most perimeter security controls did not flag it as malicious activity.
Q: Which sectors were targeted by UNC2814? UNC2814 primarily targeted telecommunications providers, internet service providers, and government agencies. These sectors hold high-value intelligence data including network infrastructure access and PII, aligning with nation-state espionage objectives.
Q: How can SOC teams detect GRIDTIDE-related activity?
Detection should focus on anomalous sheets.googleapis.com API calls from non-user devices like servers or edge appliances, unexpected SoftEther VPN installations, and high-frequency polling patterns inconsistent with normal user behavior. Cross-referencing these signals significantly increases detection confidence.
Q: What should organizations do if they suspect a GRIDTIDE compromise? Organizations should immediately isolate affected edge devices, revoke suspicious OAuth tokens, and review outbound API traffic logs for polling patterns. Compliance teams should simultaneously assess whether GDPR, HIPAA, or other applicable regulatory breach notification obligations have been triggered by the potential unauthorized access.
Enjoyed this article?
Subscribe for more cybersecurity insights.
