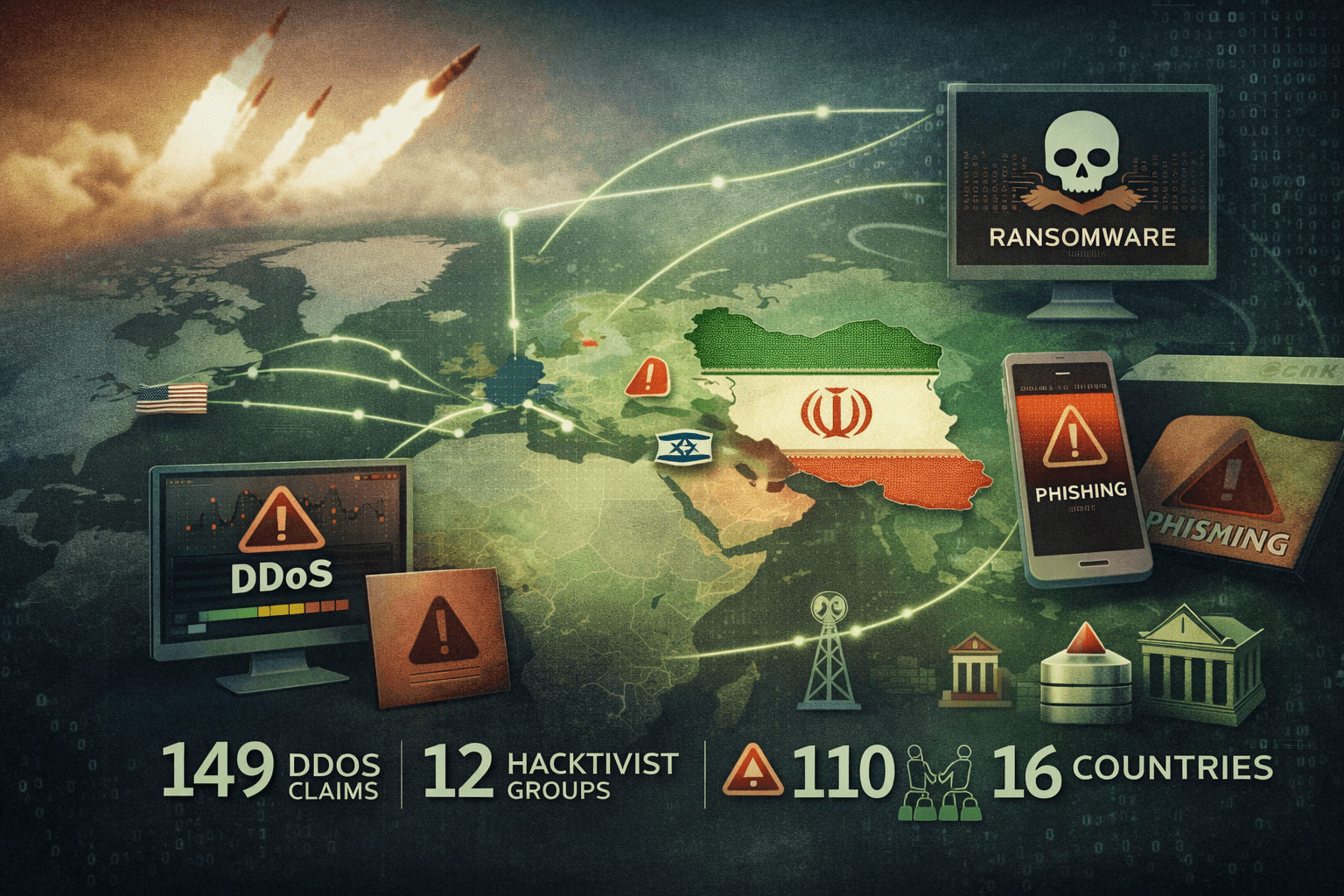
When missiles strike, keyboards follow. Within hours of U.S. and Israeli military operations against Iran—codenamed Epic Fury and Roaring Lion—a coordinated wave of hacktivist activity swept across the internet. Security researchers documented 149 Distributed Denial-of-Service (DDoS) claims from 12 hacktivist groups targeting 110 organizations across 16 countries. This is not coincidence. It is the new rhythm of modern conflict, where kinetic strikes trigger immediate cyber responses from ideologically motivated actors operating across borders and time zones.
The scale and speed of this campaign demand attention from every security team operating in government, finance, telecommunications, and critical national infrastructure (CNI). Whether your organization sits in the Middle East, Europe, or operates as a U.S. ally, you are now operating in an elevated threat environment. This post breaks down who launched these attacks, who was targeted, what tactics were used, and—most importantly—what your Cyber Incident Response Team (CIRT) needs to do right now to reduce exposure.
The Hacktivist Landscape: Who Launched These Attacks
Not all hacktivist groups operate at the same scale or with the same sophistication. Understanding the specific actors driving this campaign is essential for accurate threat modeling and prioritization.
The Leading Groups and Their Share of Activity
Three groups accounted for the majority of recorded activity. Keymous+, DieNet, and NoName057(16) collectively drove 74.6% of all DDoS claims during the campaign surge. The campaign originated on February 28, attributed to Hider Nex, a Tunisian pro-Palestine actor who also conducted hack-and-leak operations alongside volumetric attacks.
NoName057(16) is not a new name to threat intelligence analysts. This pro-Russian group has been active since 2022, consistently targeting NATO-aligned governments and infrastructure. Its participation here reflects a strategic convergence: pro-Russian and pro-Iranian hacktivist ecosystems increasingly operate in parallel, amplifying each other's claims and attack volume. Additional actors, including Cardinal and Russian Legion, made unverified claims of breaching Iron Dome-related systems—claims that, while likely overstated, warrant monitoring.
The Pro-Iranian Persona Ecosystem
Beyond the named groups, researchers from Flashpoint, Unit 42, and Nozomi Networks have tracked the expansion of pro-Iranian personas including Handala and affiliated APT Iran-linked clusters. The Islamic Revolutionary Guard Corps (IRGC) was associated with targeting Saudi Aramco infrastructure and AWS UAE-hosted assets. Meanwhile, UNC1549—a tracked Iranian state-nexus threat actor—remained active in defense and telecommunications sectors throughout the escalation period.
This layered ecosystem—combining opportunistic hacktivists, ideologically aligned proxy groups, and state-directed actors—creates attribution complexity that complicates response prioritization. Your threat intelligence team must distinguish between noise-generating DDoS claims and genuine state-sponsored intrusion activity running in parallel.
Table: Key Threat Actors and Campaign Roles
| Actor | Alignment | Primary Tactic | Verified Activity |
|---|---|---|---|
| Keymous+ | Pro-Palestine | DDoS | High |
| DieNet | Pro-Palestine | DDoS | High |
| NoName057(16) | Pro-Russia | DDoS | High |
| Hider Nex | Pro-Palestine (Tunisian) | DDoS, Hack-and-Leak | High |
| IRGC-linked | Pro-Iran | CNI targeting | Moderate |
| UNC1549 | Iranian state-nexus | Espionage, intrusion | High |
| Handala | Pro-Iran | Hack-and-Leak, disinfo | Moderate |
Target Profile: Which Sectors and Regions Face the Highest Risk
Understanding target selection patterns is critical for organizations conducting risk assessments in the current threat environment. The data from Radware and Orange Cyberdefense paints a clear geographic and sectoral picture.
Geographic Distribution of Attacks
The Middle East absorbed the heaviest concentration of activity, with 107 of 149 recorded attacks focused on the region. Within that cluster, Kuwait accounted for 28% of Middle Eastern targets, Israel 27%, and Jordan 21%. This distribution reflects the geopolitical fault lines of the conflict, with Gulf state infrastructure treated as a proxy for U.S. and Western alignment.
Europe was not spared. The continent accounted for 22.8% of global attack activity, reflecting hacktivist targeting of NATO governments, financial institutions, and telecommunications providers seen as complicit in Western support for Israeli military operations. Organizations in France, Germany, the Netherlands, and the UK reported elevated DDoS activity during the same window.
Sectoral Breakdown: Government and Finance at the Apex
Government entities bore the brunt of this campaign, representing 47.8% of all targeted organizations. This aligns with MITRE ATT&CK patterns for hacktivism: government websites and public-facing portals offer high symbolic value with relatively low technical barriers to disruption. Finance followed at 11.9%, with telecommunications at 6.7%.
Important: Financial sector organizations should note that cryptocurrency exchanges reported operational adjustments during this period due to market volatility linked to geopolitical uncertainty. This creates a dual risk: direct DDoS targeting of exchange infrastructure and opportunistic fraud activity exploiting user anxiety during price swings.
Table: Attack Distribution by Sector and Region
| Sector / Region | Share of Attacks | Risk Level | Primary Threat Vector |
|---|---|---|---|
| Government (global) | 47.8% | Critical | DDoS, defacement |
| Finance | 11.9% | High | DDoS, phishing |
| Telecommunications | 6.7% | High | DDoS, intrusion |
| Middle East (regional) | 71.8% of all | Critical | DDoS, CNI targeting |
| Europe (global) | 22.8% | High | DDoS, phishing |
| Kuwait | 28% of ME attacks | Critical | DDoS |
| Israel | 27% of ME attacks | Critical | Multi-vector |
Attack Techniques: Beyond Volumetric DDoS
While DDoS dominated the headline numbers, the full attack surface exposed during this campaign extends significantly further. Focusing exclusively on volumetric defense would leave your organization exposed to the more consequential threats running beneath the surface noise.
SMS Phishing Targeting Mobile Users
A particularly insidious tactic emerged targeting civilians and security personnel in conflict-adjacent regions: SMS phishing campaigns impersonating the RedAlert rocket alert application, a widely used emergency notification tool in Israel. Victims who clicked malicious links were served Android malware capable of credential harvesting, location tracking, and device surveillance.
This technique exploits the psychological pressure of a kinetic conflict environment—people are more likely to click emergency alerts when they believe they are in physical danger. For organizations with employees or contractors operating in the region, this represents a direct mobile device management (MDM) and endpoint security concern.
Industrial Control System and OT Risks
The UK's National Cyber Security Centre (NCSC) issued specific warnings during this period covering not only DDoS and phishing risks but also Industrial Control System (ICS) and Operational Technology (OT) targeting. Energy, water, and manufacturing organizations with IT/OT convergence should treat this warning as a direct call to action.
The concern is not hypothetical. IRGC-linked actors have demonstrated ICS targeting capability in prior campaigns, and the current escalation creates conditions where infrastructure disruption carries higher strategic value than data theft. OT networks that are not segmented from corporate IT environments represent the highest-risk exposure in this threat landscape.
Ransomware as a Retaliatory Instrument
Analysts at Halcyon have assessed that Iran may activate ransomware capabilities through proxy groups as a retaliatory mechanism in response to ongoing military pressure. This assessment, consistent with observations from SentinelOne and CrowdStrike, suggests that organizations in Israel, the United States, and close allied nations in CNI and financial services should expect potential ransomware deployment attempts—not merely nuisance-level DDoS.
Pro Tip: If your organization operates in CNI, finance, or defense-adjacent sectors in the U.S., Israel, or Europe, treat the current period as a ransomware pre-positioning window. Validate your backup integrity, test restoration procedures, and confirm that offline backup copies are not reachable from your production network.
Table: Threat Vector Risk Matrix for Current Campaign
| Threat Vector | Likelihood | Impact | Priority Mitigation |
|---|---|---|---|
| Volumetric DDoS | Very High | Medium | DDoS scrubbing, rate limiting |
| SMS phishing / mobile malware | High | High | MDM enforcement, user awareness |
| ICS / OT targeting | Moderate | Critical | IT/OT segmentation, asset inventory |
| Ransomware (proxy-deployed) | Moderate | Critical | Backup validation, EDR tuning |
| Hack-and-leak | Moderate | High | DLP, access review |
| State-sponsored espionage | Moderate | High | Network monitoring, threat hunting |
Mitigation Priorities for CIRTs and Security Teams
Sophos researchers described the surge as significant but assessed low risk of immediate large-scale escalation—a measured assessment that should inform your response posture without inducing complacency. The appropriate stance is heightened vigilance, not crisis mode. Here is how to operationalize that posture.
DDoS Resilience and Attack Surface Reduction
Your first priority is ensuring DDoS mitigation services are active, configured correctly, and tested. Many organizations have scrubbing services contracted but not validated. Now is the time to confirm:
- Traffic scrubbing capacity is provisioned for peak-load scenarios
- Rate limiting and geo-blocking rules are reviewed against current threat actor infrastructure
- Public-facing application load balancers have appropriate connection limits configured
- DNS-based DDoS protection covers all authoritative name servers for your domains
- Runbooks for DDoS escalation are current and have been rehearsed in the past 90 days
IT/OT Segmentation and ICS Hardening
For organizations with operational technology environments, the NCSC warning about ICS risks should drive immediate action aligned with NIST SP 800-82 and IEC 62443 guidance:
- Audit all network paths between corporate IT and OT/ICS networks
- Confirm that engineering workstations cannot reach the internet directly
- Validate that remote access to OT environments requires multi-factor authentication (MFA)
- Review historian and SCADA server patch levels and internet exposure
- Conduct a tabletop exercise simulating ICS-targeted attack scenarios with your OT team
Threat Intelligence Integration and Hacktivist Claim Monitoring
Not every DDoS claim translates to a successful attack—hacktivist groups frequently overclaim impact. However, monitoring claim channels provides early warning of targeting intent. Integrate feeds from Radware, Flashpoint, and Unit 42 into your Security Information and Event Management (SIEM) platform to correlate claimed targets with your organization's internet exposure profile.
Purple team exercises that stress-test DDoS resilience against realistic attack volumes are strongly recommended for CIRTs in government, finance, and telecommunications. Simulating the traffic patterns associated with NoName057(16) and DieNet provides measurable validation of your defensive posture.
Key Takeaways
- Activate DDoS scrubbing now: Validate that mitigation services are configured and tested—do not wait for an attack in progress to discover gaps
- Segment IT from OT immediately: NCSC warnings about ICS risk are not theoretical; enforce network boundaries before threat actors probe them
- Brief mobile users on SMS phishing: RedAlert-impersonating malware targets employees in conflict-adjacent regions; MDM policies and awareness training are your first line of defense
- Treat ransomware as a parallel threat: Hacktivist DDoS noise may mask pre-positioning activity; validate offline backups and test restoration procedures this week
- Monitor hacktivist claim channels: Early warning of targeting intent allows proactive posture adjustments before attacks materialize
- Distinguish actor tiers: Separate opportunistic hacktivists from state-nexus actors like UNC1549 to allocate investigative resources accurately
Conclusion
The post-strike hacktivist surge following U.S.-Israeli operations against Iran represents a new data point in the established pattern of geopolitical cyber escalation. One hundred and forty-nine DDoS claims, 110 targeted organizations, and 16 affected countries in a single campaign window illustrates how rapidly the cyber dimension of kinetic conflict mobilizes. Government entities, financial institutions, and telecommunications providers carry the highest immediate risk, while CNI operators face the more consequential long-term threat of ICS targeting and ransomware deployment through Iranian proxy networks.
The right response is neither panic nor passivity. Heightened vigilance—validated DDoS defenses, IT/OT segmentation, active threat intelligence integration, and tested incident response procedures—is the posture that separates organizations that weather these campaigns from those that become the next headline. Review your DDoS runbooks, brief your CIRT on the current actor landscape, and confirm your backup integrity before the next escalation cycle begins.
Frequently Asked Questions
Q: Which industries face the highest risk from the current hacktivist campaign? A: Government entities represent the most targeted sector at 47.8% of all attacks, followed by finance at 11.9% and telecommunications at 6.7%. Organizations in these sectors operating in the Middle East or in countries perceived as U.S. or Israeli allies—particularly in Europe—should treat the current period as an elevated risk window.
Q: Is the DDoS activity likely to escalate into more destructive attacks? A: Sophos researchers assessed the current surge as posing low risk of immediate large-scale escalation in terms of volumetric DDoS alone. However, Halcyon and CrowdStrike analysts have assessed that Iran may deploy ransomware through proxy actors as a retaliatory mechanism, meaning the threat picture extends beyond nuisance-level availability disruption.
Q: How should organizations monitor for hacktivist targeting intent? A: Integrate threat intelligence feeds from providers tracking hacktivist Telegram channels and claim boards, including Radware's Threat Intelligence feed, Flashpoint, and Unit 42. Correlating claimed targets against your organization's internet exposure profile in your SIEM allows you to identify when your sector or region is being actively discussed before an attack materializes.
Q: What is the RedAlert SMS phishing campaign and who is at risk? A: Attackers are sending SMS messages impersonating the RedAlert rocket alert application used in Israel, directing recipients to install Android malware capable of credential theft and device surveillance. Employees or contractors with devices operating in conflict-adjacent regions and organizations without enforced mobile device management (MDM) policies face the highest exposure from this tactic.
Q: How does NoName057(16)'s involvement change the threat assessment for European organizations? A: NoName057(16) has a well-documented history of targeting NATO-aligned government websites, financial institutions, and logistics infrastructure across Europe since 2022. Its participation in this campaign means European organizations—particularly in countries with vocal support for Israeli or U.S. military operations—should expect continued DDoS targeting independent of Middle Eastern geopolitical developments.
Enjoyed this article?
Subscribe for more cybersecurity insights.
