Your backup and disaster recovery infrastructure just became ground zero for nation-state espionage. A maximum-severity zero-day vulnerability in Dell RecoverPoint for Virtual Machines—tracked as CVE-2026-22769 with a CVSS score of 10.0—has been actively exploited by a suspected China-linked threat cluster since at least mid-2024. Researchers at Mandiant and Google's Threat Intelligence Group (GTIG) discovered the flaw while conducting incident response at an undisclosed victim organization and found that attackers had been operating silently for over a year before detection.
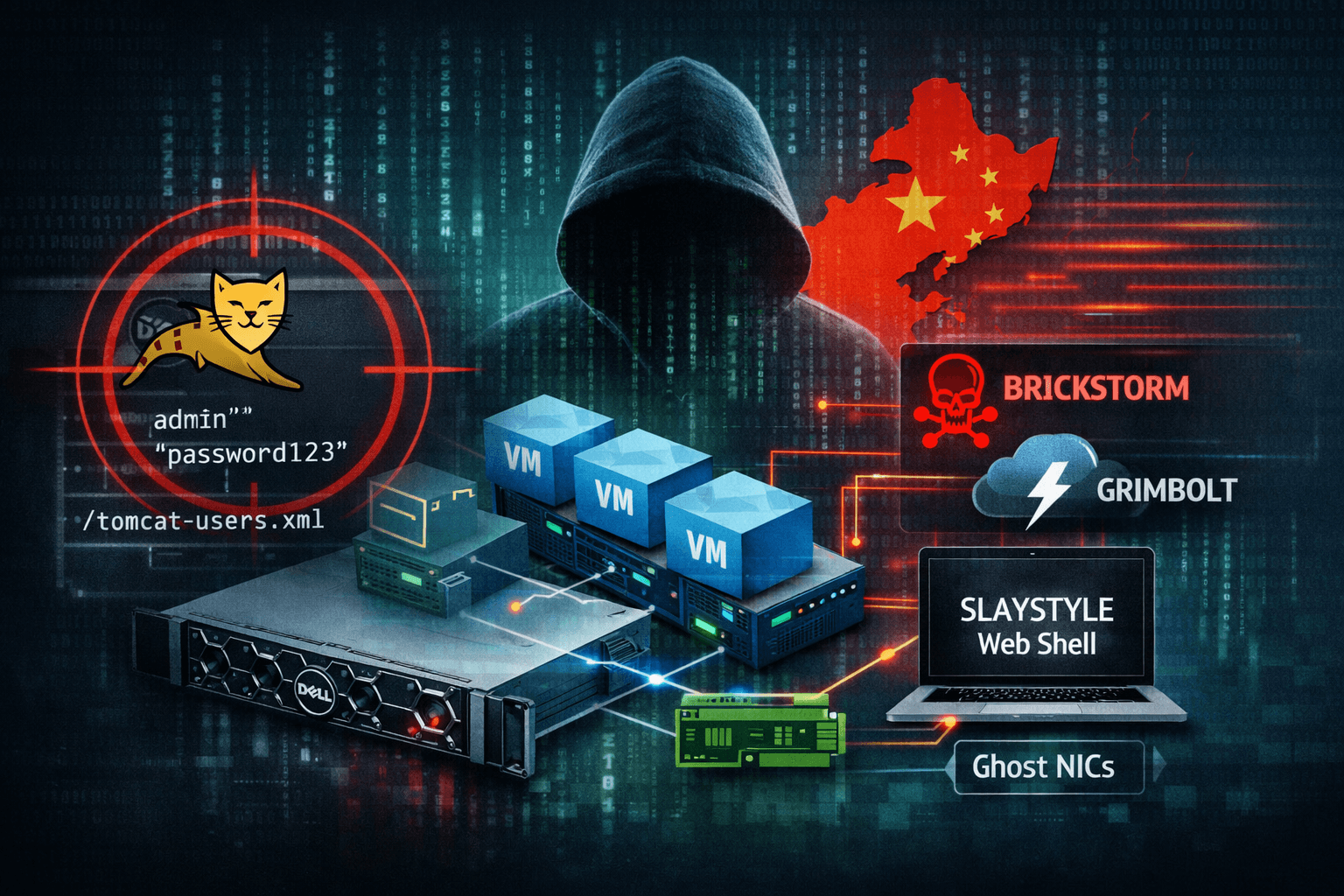
The root cause is deceptively simple: hardcoded credentials embedded in an Apache Tomcat configuration file. From that single foothold, the threat actor—designated UNC6201—deployed multiple malware families, achieved root-level persistence, and used novel techniques to pivot invisibly through VMware virtual infrastructure. CISA has since added CVE-2026-22769 to its Known Exploited Vulnerabilities (KEV) Catalog. If your organization runs Dell RecoverPoint for VMs on versions prior to 6.0.3.1 HF1, you are exposed. This article breaks down how the attack works, what makes UNC6201's tradecraft uniquely dangerous, and what you must do right now.
Understanding CVE-2026-22769: The Hardcoded Credential Trap
Hardcoded credentials represent one of the most avoidable—and most exploited—vulnerability classes in enterprise infrastructure. CVE-2026-22769 falls squarely into CWE-798 (Use of Hard-coded Credentials), where default administrative credentials for the Apache Tomcat Manager instance were embedded directly in a configuration file at /home/kos/tomcat9/conf/tomcat-users.xml.
How the Exploit Chain Operates
An unauthenticated remote attacker who knows these credentials—which are identical across all unpatched deployments—can authenticate to the Tomcat Manager interface and deploy a malicious WAR (Web Application Archive) file. UNC6201 leveraged the /manager/text/deploy endpoint to upload a web shell named SLAYSTYLE, then executed commands as root on the underlying appliance. From that position, the attackers dropped the BRICKSTORM backdoor and its successor, GRIMBOLT.
The attack chain follows a predictable sequence:
- Authenticate to Tomcat Manager using hardcoded
admincredentials - Deploy SLAYSTYLE web shell via malicious WAR file upload
- Execute root-level commands through the web shell
- Install BRICKSTORM or GRIMBOLT for persistent C2 access
- Modify
convert_hosts.shto survive reboots viarc.local - Create "Ghost NICs" to pivot deeper into VMware infrastructure
Why RecoverPoint Is a High-Value Target
Dell RecoverPoint for Virtual Machines manages backup and disaster recovery for VMware environments. Compromising it gives attackers privileged visibility into storage systems, ESXi hosts, and the entire VM lifecycle. These appliances also sit outside the typical security monitoring stack—they rarely support traditional Endpoint Detection and Response (EDR) agents, creating a blind spot that state-sponsored actors actively seek out and exploit.
Table: CVE-2026-22769 Vulnerability Profile
| Attribute | Detail |
|---|---|
| CVE ID | CVE-2026-22769 |
| CVSS Score | 10.0 (Critical) |
| Weakness | CWE-798 – Use of Hard-coded Credentials |
| Affected Versions | Dell RecoverPoint for VMs prior to 6.0.3.1 HF1 |
| Patched Version | 6.0.3.1 HF1 |
| Exploited Since | Mid-2024 |
| CISA KEV | Added February 2026 |
BRICKSTORM to GRIMBOLT: Evolving Malware Tradecraft
UNC6201's toolset demonstrates a calculated evolution designed to outpace detection and incident response. Understanding how these backdoors operate is essential for defenders building detection rules and hunting for compromise indicators.
BRICKSTORM: The Persistent Foundation
BRICKSTORM is a well-documented backdoor originally written in Go and later in Rust, designed to target appliances that lack traditional security tooling. It provides remote shell capability and command-and-control (C2) communication, and has been associated with multiple China-aligned threat clusters. CISA and CrowdStrike had previously warned organizations about BRICKSTORM activity targeting VMware vCenter environments across the legal, technology, and manufacturing sectors.
Mandiant first documented BRICKSTORM in April 2024. Its deployment on EDR-blind appliances allowed UNC6201 to maintain access inside victim networks for extended periods—in some cases, well over a year before discovery.
GRIMBOLT: The Harder-to-Detect Successor
In September 2025, investigators observed UNC6201 replacing BRICKSTORM binaries with a new backdoor: GRIMBOLT. Written in C# and compiled using native ahead-of-time (AOT) compilation, GRIMBOLT translates source code directly into native machine code before execution. This eliminates the Common Intermediate Language (CIL) metadata that static analysis tools typically use to identify malicious .NET binaries.
GRIMBOLT is also packed with UPX, an executable compressor that further reduces its static signature. It maintains the same C2 infrastructure as BRICKSTORM and adds remote shell capability, but does so in a way that leaves significantly fewer forensic traces. Mandiant's CTO of consulting described it as being better at blending in with the system's own native files.
Important: It remains unclear whether UNC6201's shift from BRICKSTORM to GRIMBOLT was a planned lifecycle upgrade or a direct response to Mandiant's incident response efforts and public disclosures. Either scenario has serious implications for how defenders should approach long-dwell intrusions.
Table: BRICKSTORM vs. GRIMBOLT Comparison
| Feature | BRICKSTORM | GRIMBOLT |
|---|---|---|
| Language | Go / Rust | C# (Native AOT) |
| Compilation | Standard | AOT + UPX packed |
| Static Detection Risk | Moderate | Low |
| Remote Shell | Yes | Yes |
| C2 Protocol | WebSocket | WebSocket (same infra) |
| Forensic Footprint | Moderate | Minimal |
| First Observed | April 2024 | September 2025 |
Ghost NICs and the VMware Pivot Technique
Beyond the initial RecoverPoint compromise, UNC6201 deployed a technique that Mandiant researchers described as previously unobserved in their investigations. The actors created temporary virtual network interfaces—dubbed "Ghost NICs"—on existing VMware ESXi virtual machines to pivot from compromised appliances into internal networks and SaaS environments.
How Ghost NICs Enable Stealthy Lateral Movement
A Ghost NIC is a temporary virtual network port attached to a running VM without going through standard provisioning workflows. UNC6201 used these ephemeral interfaces to route traffic from compromised RecoverPoint appliances into target network segments, then deleted the NICs afterward to erase evidence of the pivot. This technique exploits the flexibility of VMware's virtual networking layer to create communication paths that leave minimal logging artifacts.
The actors also used iptables rules with Single Packet Authorization (SPA) to control access to their C2 channels. SPA requires a specific "knock" packet before a port opens for communication, making passive network monitoring far less likely to capture the traffic.
Why EDR-Blind Appliances Are the Strategic Target
UNC6201's targeting pattern is deliberate and consistent with broader Chinese espionage doctrine. By focusing on backup appliances, VPN concentrators, and other edge infrastructure that does not support EDR agents, the group operates in environments where behavioral detection simply does not exist. CISA's executive assistant director for cybersecurity has publicly stated that state-sponsored actors are embedding themselves to enable long-term access, disruption, and potential sabotage—not just immediate data theft.
This campaign aligns with activity Dragos has attributed to Volt Typhoon (also tracked as Voltzite), which targeted Sierra Wireless Airlink gateways in the electric and oil and gas sectors before pivoting to engineering workstations.
Table: UNC6201 MITRE ATT&CK Technique Mapping
| Technique ID | Name | Implementation |
|---|---|---|
| T1078 | Valid Accounts | Hardcoded Tomcat admin credentials |
| T1505.003 | Web Shell | SLAYSTYLE via malicious WAR deployment |
| T1105 | Ingress Tool Transfer | BRICKSTORM and GRIMBOLT payload delivery |
| T1547 | Boot/Logon Autostart | Persistence via convert_hosts.sh + rc.local |
| T1071 | Application Layer Protocol | WebSocket-based C2 communications |
| T1562 | Impair Defenses | Ghost NIC creation and deletion to erase pivoting evidence |
Detection, Hunting, and Immediate Remediation Steps
The scale of known CVE-2026-22769 compromises remains limited—Mandiant has confirmed fewer than a dozen affected organizations—but the group has had over 18 months to establish persistence inside undetected environments. That dwell time demands aggressive hunting, not just patching.
Patch and Remediation Priority
Dell has released version 6.0.3.1 HF1 as the definitive remediation for CVE-2026-22769. Organizations that cannot immediately apply the patch should apply Dell's remediation script available via the official support knowledge base article. This is not optional; CISA's KEV listing means federal agencies face a mandatory remediation deadline, and private organizations should treat the urgency equivalently.
Remediation steps in order of priority:
- Upgrade to Dell RecoverPoint for VMs version 6.0.3.1 HF1 immediately
- Apply Dell's remediation script if patching is temporarily infeasible
- Rotate all credentials associated with RecoverPoint appliances and connected VMware systems
- Audit Tomcat configuration files across all RecoverPoint deployments for unauthorized changes
- Review
convert_hosts.shandrc.localfor unauthorized modifications
Threat Hunting Indicators
Organizations previously exposed to BRICKSTORM must actively hunt for GRIMBOLT in their environments. The malware uses the same C2 infrastructure, so prior BRICKSTORM indicators of compromise (IoCs) remain relevant. Key artifacts to hunt for include:
- Web requests to the Tomcat Manager endpoint (
/manager/text/deploy) using theadminusername - Presence of WAR files in
/var/lib/tomcat9or/var/cache/tomcat9/Catalina - Modifications to
/home/kos/kbox/src/installation/distribution/convert_hosts.sh - Unexpected
iptablesrules involving string-matching hex patterns - Transient network interfaces on ESXi VMs with no corresponding provisioning records
- Outbound WebSocket connections from RecoverPoint appliances to unknown external hosts
Pro Tip: YARA rules for detecting GRIMBOLT and SLAYSTYLE have been published by GTIG in a free collection for registered users. Deploy these rules in your SIEM or EDR platforms immediately. BRICKSTORM SHA-256 hashes and the network indicator 149.248.11.71 are also publicly available for blocking and hunting.
UNC6201 Threat Actor Context
UNC6201 shows notable tactical overlaps with UNC5221, a cluster associated with exploitation of Ivanti zero-days and sometimes conflated with the threat group publicly reported as Silk Typhoon. GTIG does not currently assess the two clusters as identical. CrowdStrike has separately linked BRICKSTORM usage to a third China-aligned group it tracks as Warp Panda, indicating that this toolset has been shared or borrowed across multiple PRC-nexus actors.
Key Takeaways
- Patch immediately: Upgrade all Dell RecoverPoint for VMs deployments to version 6.0.3.1 HF1 or apply Dell's interim remediation script without delay
- Hunt for GRIMBOLT now: Any organization previously targeted by BRICKSTORM must actively search for GRIMBOLT using published YARA rules and IoCs
- Audit appliance persistence mechanisms: Review
convert_hosts.sh,rc.local, and Tomcat configuration files on all RecoverPoint systems for unauthorized modifications - Extend visibility to EDR-blind assets: Implement network-level monitoring, log forwarding, and anomaly detection for backup appliances and other non-EDR infrastructure
- Monitor VMware for Ghost NICs: Audit virtual network interface creation logs on ESXi hosts for transient interfaces that lack corresponding provisioning records
- Block known network indicators: Apply firewall rules against published UNC6201 C2 infrastructure and enable alerting on outbound WebSocket connections from appliance networks
Conclusion
CVE-2026-22769 is a textbook example of how a single architectural flaw—hardcoded credentials in a configuration file—can become a nation-state entry point into the deepest layers of enterprise infrastructure. UNC6201 did not need sophisticated exploitation techniques. They needed only a username and password that never should have existed in the first place, and then they spent 18 months using it.
The BRICKSTORM-to-GRIMBOLT evolution shows that this threat cluster is actively adapting to incident response pressure and investing in harder-to-detect tooling. The introduction of Ghost NICs demonstrates a willingness to develop novel techniques specifically to exploit virtualization platform weaknesses. For virtualization and OT defenders, this campaign is a clear signal: backup and recovery infrastructure is not a secondary security concern. It is a primary target. Apply the patch, hunt for compromise, and treat your EDR-blind appliances as the attack surface they have already become.
Frequently Asked Questions
Q: What versions of Dell RecoverPoint for VMs are vulnerable to CVE-2026-22769?
A: All versions prior to 6.0.3.1 HF1 are affected. Dell has released this hotfix as the official patch, and organizations unable to apply it immediately should use Dell's published remediation script as an interim measure.
Q: How did UNC6201 gain initial access to victim environments before exploiting CVE-2026-22769?
A: The initial access vector was not confirmed in Mandiant's investigation. However, UNC6201 is known for targeting edge appliances such as VPN concentrators to gain an initial foothold, consistent with broader China-nexus intrusion patterns observed by GTIG.
Q: What is the difference between BRICKSTORM and GRIMBOLT?
A: Both backdoors provide remote shell capability and use the same C2 infrastructure, but GRIMBOLT is compiled in C# using native ahead-of-time (AOT) compilation and packed with UPX. This makes GRIMBOLT significantly harder to detect through static analysis and leaves fewer forensic artifacts than its Go/Rust-based predecessor.
Q: What are "Ghost NICs" and why do they matter for defenders?
A: Ghost NICs are temporary virtual network interfaces that UNC6201 created on VMware ESXi virtual machines to pivot from compromised RecoverPoint appliances into internal or SaaS environments. After pivoting, the actor deleted the interfaces to remove evidence. Defenders should monitor ESXi host logs for transient NIC creation events that lack corresponding change management records.
Q: Is CVE-2026-22769 on CISA's Known Exploited Vulnerabilities catalog?
A: Yes. CISA added CVE-2026-22769 to its KEV Catalog in February 2026, following Dell's disclosure and Mandiant's publication of the campaign details. Federal agencies face mandatory remediation deadlines under Binding Operational Directive 22-01, and all organizations should treat the KEV listing as a high-priority remediation signal.
Enjoyed this article?
Subscribe for more cybersecurity insights.
