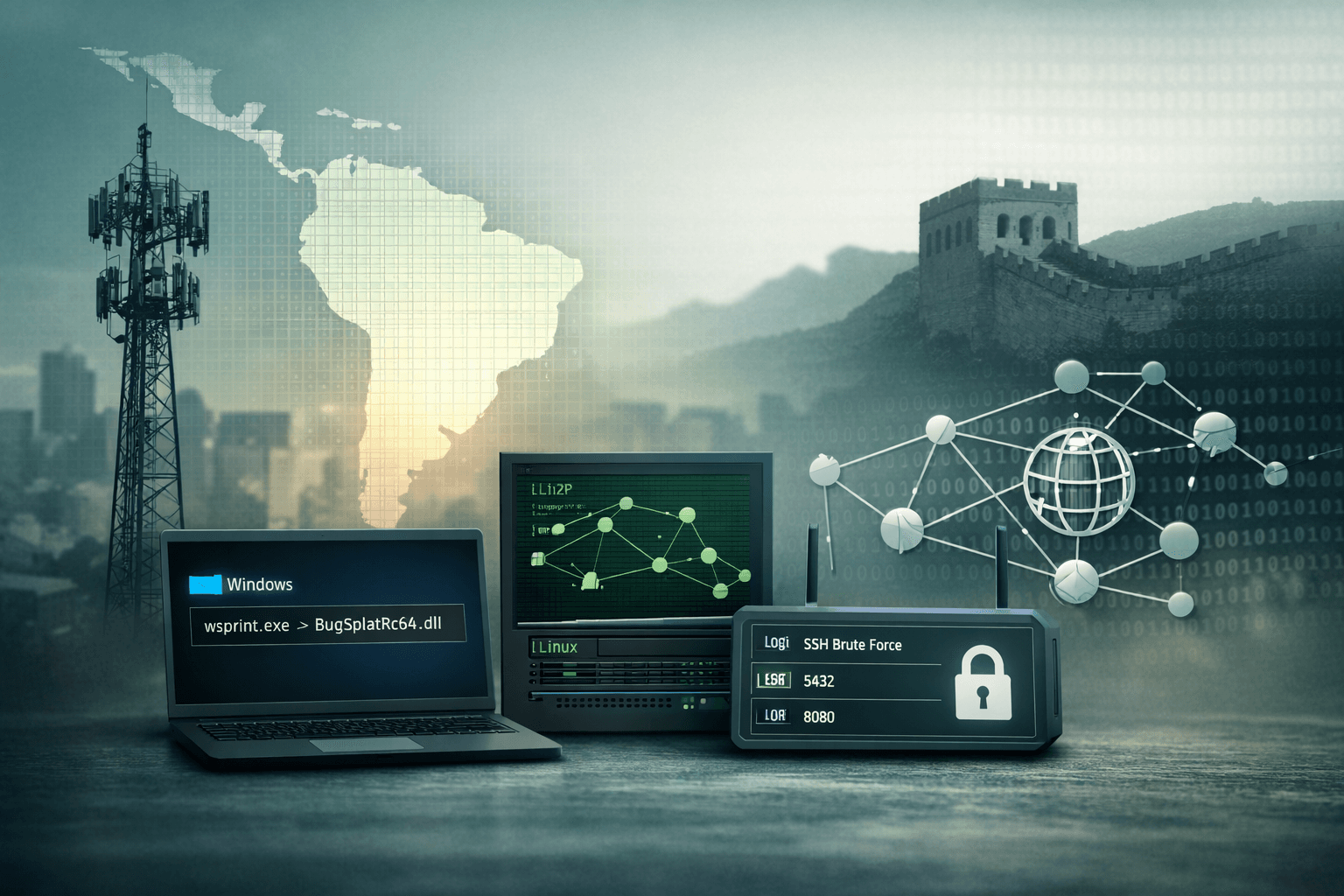
A state-sponsored threat actor has been systematically dismantling South American telecommunications infrastructure — and most defenders never saw it coming. Since 2024, Cisco Talos researchers have tracked UAT-9244, a China-nexus advanced persistent threat (APT) group with confirmed overlaps to FamousSparrow, targeting regional telecoms with a multi-platform toolset specifically engineered to evade detection. The stakes could not be higher: telecommunications providers underpin every layer of critical national infrastructure (CNI), from emergency services to financial systems.
What makes UAT-9244 uniquely dangerous is its operational sophistication. This group deploys three purpose-built malware families across Windows, Linux, and edge devices simultaneously, uses peer-to-peer (P2P) command-and-control (C2) communications to blend into legitimate traffic, and scales brute-force operations through operational relay box (ORB) proxy networks. Infrastructure overlaps with Salt Typhoon — the group behind the 2024 U.S. telecom espionage campaign — suggest shared tooling or coordinated tasking.
This post breaks down UAT-9244's toolset, tactics, techniques, and procedures (TTPs), maps them to MITRE ATT&CK, and provides actionable detection and mitigation guidance for telecom security teams.
UAT-9244's Three-Tool Arsenal: A Multi-Platform Threat
UAT-9244 does not rely on a single implant. Instead, the group deploys three distinct malware families, each targeting a specific platform and fulfilling a distinct role in the kill chain. This modular approach maximizes coverage and resilience.
TernDoor: Windows Persistence via DLL Side-Loading
TernDoor is a Windows dynamic-link library (DLL) implant identified as a variant of CrowDoor malware. It achieves initial execution through DLL side-loading — a technique that abuses legitimate signed executables to load malicious code. Specifically, UAT-9244 weaponizes wsprint.exe and BugSplatRc64.dll to deliver the payload without triggering standard antivirus detections.
Once active, TernDoor establishes persistence through two redundant mechanisms:
- Windows Scheduled Tasks (T1053.005)
- Registry Run keys under
HKCU\Software\Microsoft\Windows\CurrentVersion\Run(T1547.001)
The implant then injects into msiexec.exe, a trusted Windows Installer process, to mask its network activity. From there, it decrypts its C2 configuration, executes remote commands, manages files and processes, and uses a kernel-level driver to hide its presence from process listings and security tooling.
Important: TernDoor's use of
msiexec.exeinjection means process-based allow lists alone are insufficient. Behavioral analytics trackingmsiexec.exeinitiating outbound connections are essential.
PeerTime: Linux P2P Command-and-Control
PeerTime is UAT-9244's Linux implant and its most innovative component. Rather than relying on traditional HTTP/S C2 beaconing — which network security tools readily detect — PeerTime uses a BitTorrent-style P2P protocol to communicate with operators and transfer files.
The loader first checks for Docker runtime environments, suggesting the group deliberately targets containerized infrastructure. It then decrypts Executable and Linkable Format (ELF) payloads written in both C++ and Rust, providing resilience through language diversity.
PeerTime's cross-architecture support is particularly notable:
Table: PeerTime Supported Architectures
| Architecture | Common Targets | Detection Difficulty |
|---|---|---|
| x86/x64 | Standard Linux servers | Medium |
| ARM / AARCH64 | IoT, edge routers, Raspberry Pi | High |
| PowerPC (PPC) | Legacy telco switching hardware | Very High |
| MIPS | Embedded networking devices | Very High |
The implant renames its processes to blend into system process lists, then leverages the BitTorrent DHT (Distributed Hash Table) network for C2 commands and file transfers — traffic that virtually no enterprise firewall blocks by default.
BruteEntry: Golang-Based ORB-Powered Credential Brute-Forcer
BruteEntry is a Golang-compiled tool deployed on ORB proxy nodes. Its sole mission is credential brute-forcing at scale across three high-value protocols:
- PostgreSQL database servers (port 5432)
- SSH remote access (port 22)
- Apache Tomcat management interfaces (ports 8080/8443)
BruteEntry reports successful credential compromises back to its C2, feeding a pipeline of initial access opportunities. The use of ORB proxies — compromised third-party infrastructure scattered globally — makes attribution and IP-based blocking ineffective.
Initial Access and Infrastructure: Exchange Servers and Salt Typhoon Overlaps
How does UAT-9244 get its foot in the door? Cisco Talos researchers note evidence of prior Microsoft Exchange webshells on older, unpatched servers within victimized organizations. This aligns with a well-documented pattern among China-nexus APTs: exploit known Exchange vulnerabilities (ProxyShell, ProxyLogon, and their successors) before organizations apply patches.
The Salt Typhoon Connection
Infrastructure analysis reveals meaningful overlaps between UAT-9244 and Salt Typhoon (also tracked as GhostEmperor/FamousSparrow depending on cluster), the group behind 2024's sweeping U.S. telecommunications espionage campaign. These overlaps include shared C2 IP ranges and common tooling lineage.
This relationship has serious implications. Salt Typhoon's documented mission is signals intelligence collection — intercepting voice, SMS, and lawful intercept systems. UAT-9244 targeting South American telecoms with overlapping infrastructure suggests a coordinated, geopolitically motivated campaign amid rising U.S.-China tensions in the region.
The ORB Network Advantage
ORB proxy networks fundamentally change the threat landscape for defenders. Traditional threat intelligence that blocks known malicious IP addresses becomes largely irrelevant when attackers route through hundreds of compromised residential and commercial nodes.
Table: Traditional C2 vs. ORB-Based Infrastructure
| Attribute | Traditional C2 | ORB Proxy Network |
|---|---|---|
| IP Reputation | Often flagged | Appears legitimate |
| Attribution Speed | Days to weeks | Weeks to months |
| Takedown Impact | High | Low (distributed) |
| Block Effectiveness | High | Low |
| Detection Method | IP/domain IOCs | Behavioral analytics |
MITRE ATT&CK Mapping and Threat Hunting Priorities
Understanding UAT-9244 through the MITRE ATT&CK framework enables structured detection engineering. Security teams should prioritize building detections for the following technique clusters.
High-Priority ATT&CK Techniques
Table: UAT-9244 MITRE ATT&CK Coverage
| Technique ID | Technique Name | Malware | Detection Priority |
|---|---|---|---|
| T1574.002 | DLL Side-Loading | TernDoor | Critical |
| T1055.001 | Process Injection (msiexec) | TernDoor | Critical |
| T1547.001 | Registry Run Keys | TernDoor | High |
| T1053.005 | Scheduled Tasks | TernDoor | High |
| T1090.003 | Multi-hop Proxy (ORB) | BruteEntry | High |
| T1110.001 | Password Brute Force | BruteEntry | Medium |
| T1071 | Application Layer Protocol (P2P) | PeerTime | Critical |
| T1611 | Escape to Host (Docker) | PeerTime | High |
Blue Team Detection Guidance
For defenders, several behavioral indicators should immediately trigger investigation:
msiexec.exeestablishing outbound connections to non-Microsoft IP ranges- Scheduled tasks with encoded or obfuscated command lines created outside patch windows
- BitTorrent DHT traffic originating from server-class Linux hosts
- PostgreSQL authentication failures followed by rapid success from the same external IP
- Docker container processes spawning unexpected child processes or network connections
- New DLL files appearing in directories alongside signed executables like
wsprint.exe
Pro Tip: Audit your Endpoint Detection and Response (EDR) telemetry specifically for
BugSplatRc64.dllhash variants and any unsigned DLL loaded by processes in your telemetry. TernDoor's side-load chain is a highly detectable artifact if you hunt proactively.
Red Team Emulation Scenarios
Red teams assessing telecom environments should emulate TernDoor's DLL side-loading chain as a tabletop or purple team exercise. Key validation questions include: Does your EDR alert on unsigned DLLs loaded by signed executables? Does your SIEM detect msiexec.exe network anomalies? Can your SOC distinguish BitTorrent traffic from production servers versus workstations?
Mitigation Priorities for Telecom Security Teams
Given UAT-9244's confirmed targeting of telecommunications CNI, security teams should treat this threat with the same urgency as a Known Exploited Vulnerability (KEV) advisory. The following mitigations address the group's documented TTPs.
Immediate Patch and Hardening Actions
- Patch Microsoft Exchange immediately — Apply all available Cumulative Updates (CUs) and security patches. Audit for webshells using Microsoft's MSERT scanner or equivalent.
- Segment edge devices — Place routers, firewalls, and VPN concentrators in isolated network segments with restrictive east-west traffic policies.
- Disable unnecessary services — Remove Apache Tomcat management interfaces from internet exposure; enforce key-based SSH authentication and disable password auth.
- Harden PostgreSQL — Restrict pg_hba.conf to explicit IP ranges; enforce strong password policies and consider certificate-based authentication.
- Audit Docker deployments — Implement runtime security monitoring; review container-to-host network policies.
Compliance Framework Alignment
Organizations operating under GDPR, HIPAA, or PCI DSS face elevated regulatory risk from UAT-9244 compromise. Telecom providers subject to NIST SP 800-53 or ISO 27001 should treat this advisory as a trigger for formal risk reassessment. CIS Controls v8 Controls 4 (Secure Configuration), 7 (Continuous Vulnerability Management), and 13 (Network Monitoring) are directly applicable.
Key Takeaways
- Patch Exchange servers now — UAT-9244's likely initial access vector is legacy Exchange vulnerabilities; treat unpatched servers as compromised.
- Monitor BitTorrent traffic from servers — PeerTime's P2P C2 bypasses traditional network controls; server-to-DHT communications are a critical detection signal.
- Deploy behavioral EDR rules for
msiexec.exeoutbound connections and DLL side-loading patterns indicative of TernDoor. - Block password-based authentication on SSH, Tomcat, and PostgreSQL to neutralize BruteEntry's brute-force capability.
- Segment your edge devices — compromised routing infrastructure enables the ORB networks UAT-9244 relies on for stealthy operations.
- Brief your CISO on Salt Typhoon overlaps — UAT-9244's infrastructure ties suggest mission alignment with signals intelligence collection, elevating the threat to your lawful intercept and core network systems.
Conclusion
UAT-9244 represents a new standard of sophistication in state-sponsored telecom espionage. By combining DLL side-loading on Windows, P2P C2 on Linux, and ORB-powered brute-forcing on edge devices, this China-nexus group has built a toolchain that defeats most single-layer security controls. Its confirmed overlaps with Salt Typhoon signal that South American telecommunications providers may be early targets in a broader regional intelligence collection campaign.
The good news is that UAT-9244's TTPs are detectable — if defenders know where to look. Exchange patch status, msiexec.exe behavioral analytics, BitTorrent traffic from servers, and credential brute-force patterns are all measurable signals. Your threat hunting program should prioritize these indicators today.
Start by validating your Exchange patch posture, reviewing EDR coverage for DLL side-loading, and auditing network egress policies for P2P protocols. The window to detect and evict this actor before significant damage occurs remains open — but it will not stay open indefinitely.
Frequently Asked Questions
Q: What industries beyond telecommunications are at risk from UAT-9244?
A: While Cisco Talos has specifically documented UAT-9244 targeting South American telecoms, the group's toolset is platform-agnostic and well-suited for any CNI sector. Organizations in energy, finance, and government with legacy Windows environments, Linux infrastructure, and internet-exposed edge devices should treat this advisory as relevant to their threat model.
Q: How does PeerTime's BitTorrent C2 evade traditional network security tools?
A: Most enterprise firewalls and proxies do not block BitTorrent DHT protocol traffic by default, since it's commonly used for legitimate file sharing. PeerTime exploits this gap by encoding C2 commands and file transfers within standard torrent peer communications, making the traffic indistinguishable from legitimate BitTorrent activity without deep packet inspection tuned to server-source anomalies.
Q: What is the relationship between UAT-9244 and FamousSparrow or Salt Typhoon?
A: Cisco Talos identifies behavioral and infrastructure overlaps between UAT-9244, FamousSparrow, and Salt Typhoon, suggesting shared tooling, infrastructure reuse, or coordinated tasking under a broader Chinese state-sponsored umbrella. These clusters may represent distinct teams operating under the same intelligence directive rather than a single unified group.
Q: How should we prioritize UAT-9244 mitigations against other active threats?
A: Organizations in telecommunications or CNI-adjacent sectors should treat UAT-9244 as a Priority 1 threat due to its confirmed targeting, CNI focus, and Salt Typhoon infrastructure overlaps. If your Exchange servers are unpatched or your edge devices expose SSH and database management ports externally, those remediations should occur within your current sprint cycle.
Q: Are there specific IOCs available for EDR hunting?
A: Cisco Talos has published indicators of compromise (IOCs) associated with UAT-9244, including file hashes for TernDoor DLL variants, PeerTime ELF samples across architectures, and BruteEntry Golang binaries. Security teams should ingest these IOCs into their SIEM and EDR platforms immediately and set up retrospective hunts across 90-180 days of telemetry to identify potential prior compromise.
Enjoyed this article?
Subscribe for more cybersecurity insights.
