A nation-state threat actor just weaponized a critical Windows vulnerability before most organizations had a chance to patch it. In January 2026, Russia-linked APT28 (also tracked as Fancy Bear and Forest Blizzard) actively exploited CVE-2026-21513, a high-severity flaw in Microsoft's MSHTML engine, targeting government and defense sector organizations — many with ties to ongoing Ukraine-focused campaigns. The vulnerability carries a CVSS score of 8.8, reflecting its low attack complexity and significant impact on confidentiality and integrity.
This is not a theoretical risk. Malicious files were uploaded to VirusTotal on January 30, 2026, weeks before Microsoft's February Patch Tuesday addressed the flaw. CERT-UA has linked related activity to a companion Office vulnerability, CVE-2026-21509, suggesting a coordinated, multi-vector campaign.
This article breaks down exactly how CVE-2026-21513 works, how APT28 weaponized it, what defenders need to do immediately, and how red teams can use this scenario to test their own evasion detection capabilities.
Understanding CVE-2026-21513: The MSHTML ieframe.dll Flaw
MSHTML — the rendering engine historically powering Internet Explorer (IE) and still embedded in Windows components — remains a persistent attack surface despite IE's official retirement. CVE-2026-21513 exposes a critical weakness in ieframe.dll, the library responsible for handling hyperlink navigation within MSHTML-rendered content.
How the Vulnerability Works
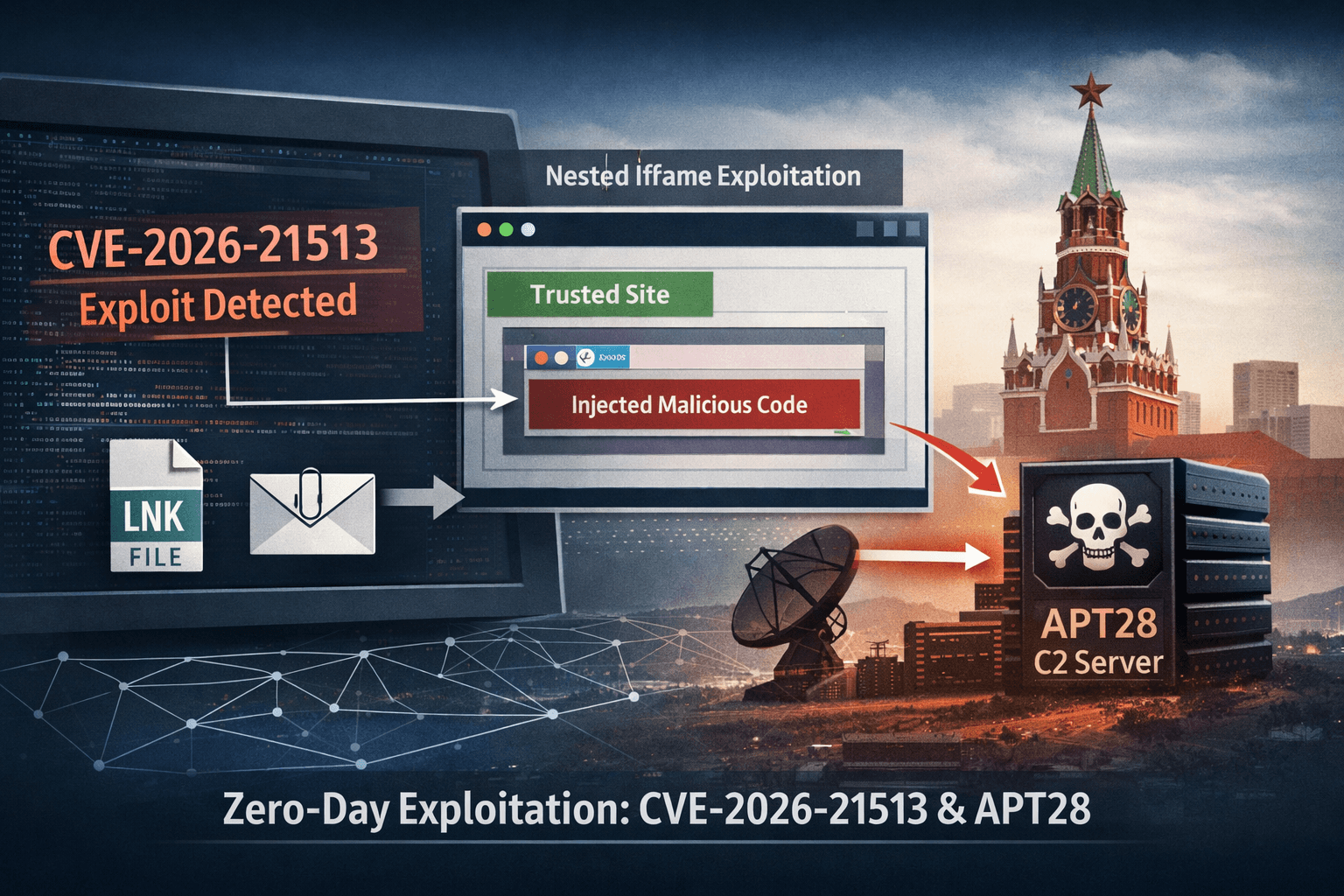
The flaw stems from improper handling of hyperlink navigation events within ieframe.dll. When a specially crafted LNK file or HTML document triggers a navigation sequence, the engine fails to correctly enforce security zone boundaries. This allows an attacker to invoke ShellExecuteExW — a Windows API call that launches external processes or opens files — without triggering expected security warnings.
Under normal circumstances, the Mark-of-the-Web (MotW) mechanism flags files downloaded from the internet, prompting user warnings before execution. Similarly, Internet Explorer Enhanced Security Configuration (IE ESC) applies restrictions to embedded web content. CVE-2026-21513 bypasses both controls through a nested iframe technique that confuses the security zone resolution logic.
The Nested iframe Bypass Technique
Akamai's analysis of the exploit reveals a layered evasion method:
- An outer iframe loads a trusted or neutral resource to establish a permissive zone context
- Inner nested iframes load the malicious payload within that inherited context
- The zone mismatch causes MSHTML to skip MotW and IE ESC validation
ShellExecuteExWis invoked against attacker-controlled content without user-visible prompts
This technique effectively achieves a browser sandbox bypass, allowing arbitrary resource execution on the victim host.
Table: CVE-2026-21513 Vulnerability Profile
| Attribute | Detail |
|---|---|
| CVE ID | CVE-2026-21513 |
| CVSS Score | 8.8 (High) |
| Affected Component | MSHTML / ieframe.dll |
| Attack Vector | Network (user interaction required) |
| Security Bypasses | Mark-of-the-Web, IE ESC |
| Execution Method | ShellExecuteExW |
| Patch Availability | February 2026 Patch Tuesday |
APT28's Weaponization: From LNK Files to Multistage Payloads
APT28 is a Russian military intelligence (GRU) unit with a decade-long track record of targeting government, military, and critical infrastructure organizations across NATO member states. Their exploitation of CVE-2026-21513 follows a well-established phishing-to-persistence playbook — but with notable technical refinements.
The Malicious LNK Delivery Chain
The primary initial access vector identified uses a malicious LNK file — a Windows shortcut — embedding an HTML payload directly within its structure. When a victim opens the LNK (often delivered via spear-phishing email or compromised file shares), the embedded HTML loads silently within the MSHTML context.
The HTML payload communicates with APT28-controlled infrastructure. Researchers identified the domain wellnesscaremed[.]com as part of this command-and-control (C2) network. The domain follows APT28's established pattern of registering legitimately-sounding domains to blend into network traffic.
The payload stages proceed as follows:
- LNK file opened by victim triggers MSHTML rendering
- Embedded HTML exploits CVE-2026-21513 to bypass MotW and IE ESC
ShellExecuteExWexecutes a second-stage downloader- Downloader contacts APT28 C2 infrastructure
- Final payload (likely credential harvester or implant) deploys
CERT-UA Attribution and CVE-2026-21509 Linkage
Ukraine's Computer Emergency Response Team (CERT-UA) linked this campaign to a parallel exploitation effort using CVE-2026-21509, a related Microsoft Office vulnerability. The dual-vulnerability approach increases the likelihood of successful compromise — if one delivery mechanism is blocked, the other may succeed.
Important: CERT-UA's attribution and the VirusTotal upload date of January 30, 2026 confirm that APT28 exploited this vulnerability as a zero-day, with no public patch available at the time of active exploitation.
Table: APT28 CVE-2026-21513 Campaign Overview
| Indicator | Detail |
|---|---|
| Threat Actor | APT28 / Fancy Bear / Forest Blizzard (GRU) |
| Initial Access | Malicious LNK file via spear-phishing |
| C2 Domain (IOC) | wellnesscaremed[.]com |
| Related Vulnerability | CVE-2026-21509 (Microsoft Office) |
| First VirusTotal Upload | January 30, 2026 |
| Patch Date | February 2026 Patch Tuesday |
| Primary Targets | Government, defense, Ukraine-linked entities |
| Disclosure Credit | MSTIC, MSRC, GTIG |
Detection and Threat Hunting Strategies
Patching eliminates the vulnerability, but you still need to determine whether your environment was compromised before you patched. Active threat hunting for APT28 TTPs (Tactics, Techniques, and Procedures) mapped to MITRE ATT&CK is essential for any organization in the government or defense sector.
Anomalous ShellExecute Detection
The most direct detection opportunity is monitoring for unusual ShellExecuteExW invocations originating from MSHTML-related processes. Key hunting queries should target:
iexplore.exe,mshtml.dll, orieframe.dllas parent or caller contextShellExecuteExWcalls spawning unexpected child processes- Child processes with no MotW attributes in environments where downloads are standard
- Outbound connections from Office or browser-embedded components to newly registered domains
Endpoint Detection and Response (EDR) platforms with process lineage visibility are the most effective tools here. Correlate ShellExecuteExW telemetry with network connections to unknown or low-reputation external IPs.
APT28 IOC Hunting
Beyond the technical vulnerability indicators, hunt for known APT28 behavioral patterns aligned with MITRE ATT&CK T1566.001 (Spearphishing Attachment) and T1218 (Signed Binary Proxy Execution):
- DNS queries or connections to wellnesscaremed[.]com and related APT28 infrastructure
- LNK files in unusual locations (Temp folders, AppData, email attachments)
- MSHTML processes initiating outbound HTTPS connections
- Registry persistence entries created by unexpected parent processes
Pro Tip: If your SIEM does not currently alert on ShellExecuteExW from Office or MSHTML process contexts, add that rule immediately. This is a high-fidelity signal for this and similar MSHTML-abuse techniques.
Logging Enhancements for Blue Teams
Defenders should verify that the following telemetry sources are active and feeding into their SIEM:
- Windows Process Creation (Event ID 4688) with command-line logging enabled
- Sysmon Event ID 1 for process creation with full image path
- Sysmon Event ID 3 for network connections from browser/Office processes
- PowerShell Script Block Logging for any post-exploitation script activity
- Windows Defender Application Control (WDAC) audit logs for unsigned binary execution
Patching, Prioritization, and Risk Assessment
The February 2026 Patch Tuesday update addresses CVE-2026-21513. Given active exploitation by a nation-state actor prior to patch release, this vulnerability demands emergency patching priority in any organization running Windows systems that embed MSHTML components.
Affected Scope Beyond LNK Files
Akamai's research notes that while the LNK delivery vector is the confirmed exploitation method, the underlying MSHTML flaw may support additional delivery mechanisms. Organizations should not assume that blocking LNK file execution alone fully mitigates exposure. Other potential vectors include:
- Malicious HTML files delivered via email or web downloads
- Embedded MSHTML content in Office documents (relevant given CVE-2026-21509 linkage)
- Drive-by scenarios targeting applications that invoke MSHTML for rendering
This broader attack surface underscores the urgency of applying the official patch rather than relying solely on workarounds.
Compliance Implications
Organizations subject to regulatory frameworks face additional pressure to act quickly. Active exploitation by a nation-state actor triggers incident response and notification obligations under several standards:
Table: Compliance Frameworks and Patch Urgency
| Framework | Relevant Control | Implication |
|---|---|---|
| NIST CSF 2.0 | RS.MI-3 (Mitigation) | Patch as critical mitigation action |
| ISO 27001 | A.12.6.1 (Technical Vulnerability Mgmt) | Document patching timeline and exceptions |
| CIS Controls | Control 7 (Continuous Vuln Management) | Prioritize CVSS 8.8 within 24–72 hours |
| GDPR | Article 32 (Security of Processing) | Assess for reportable breach if compromised |
| HIPAA | 164.308(a)(5) (Security Awareness) | Evaluate if ePHI systems are exposed |
| PCI DSS v4 | Req. 6.3 (Security Vulnerabilities) | Critical patches within defined remediation SLA |
Guidance for Red Teams: Replicating the Evasion Technique
This exploitation scenario provides a valuable benchmark for red team engagements testing detection of MSHTML abuse and LNK-based phishing. Replicating the core technique — nested iframe zone confusion leading to ShellExecuteExW invocation — allows security teams to validate whether their endpoint and network controls would catch APT28-style activity.
Key Red Team Test Scenarios
- Craft a LNK file that invokes an MSHTML rendering context and observe EDR alerting behavior
- Test whether your email gateway strips or flags LNK attachments (many do not by default)
- Simulate C2 beacon traffic to a newly registered domain and measure detection latency
- Validate that ShellExecute from MSHTML contexts triggers an alert in your SIEM
Alignment with MITRE ATT&CK
Red team scenarios should map to the following techniques to ensure detection coverage validation is comprehensive:
- T1566.001 – Spearphishing Attachment (LNK delivery)
- T1218 – Signed Binary Proxy Execution
- T1203 – Exploitation for Client Execution
- T1071.001 – Application Layer Protocol: Web Protocols (C2 over HTTPS)
- T1574 – Hijack Execution Flow (ShellExecuteExW abuse)
Key Takeaways
- Patch immediately: Apply the February 2026 Patch Tuesday update — CVE-2026-21513 was actively exploited as a zero-day before the fix was available.
- Hunt retroactively: Search your environment for ShellExecuteExW anomalies and APT28 IOCs, including wellnesscaremed[.]com, for activity predating your patch date.
- Enhance MSHTML logging: Enable Sysmon process creation and network connection events specifically for MSHTML and Office component processes.
- Block LNK attachments at the email gateway: If your organization has no legitimate use case for LNK attachments in email, block them outright.
- Treat this as a multi-vector campaign: The linkage to CVE-2026-21509 means LNK mitigation alone is insufficient — assess your Office document rendering exposure as well.
- Validate red team coverage: Use this scenario to test whether your current controls detect nested iframe zone confusion and anomalous ShellExecute invocations.
Conclusion
CVE-2026-21513 is a stark reminder that legacy components like MSHTML continue to carry significant risk long after their primary use cases fade. APT28's exploitation of this vulnerability — combining a sophisticated bypass of Mark-of-the-Web and IE ESC with a multistage LNK delivery chain — reflects the group's consistent operational maturity and focus on high-value government and defense targets.
The window between zero-day exploitation and patch availability was real and measurable. Organizations that patch promptly, hunt aggressively, and invest in telemetry for MSHTML process behavior are best positioned to minimize exposure. The February 2026 patch closes this specific door, but Akamai's research suggests that variant techniques targeting non-LNK delivery vectors may follow. Stay ahead of that curve by treating MSHTML as a persistent attack surface requiring active monitoring — not a retired technology safely ignored.
Frequently Asked Questions
Q: What systems are affected by CVE-2026-21513?
A: Any Windows system that embeds the MSHTML rendering engine is potentially affected. This extends beyond Internet Explorer to any application or Windows component that uses MSHTML for rendering HTML content, including certain Office components and custom applications invoking the engine programmatically.
Q: Has Microsoft released a patch for CVE-2026-21513?
A: Yes. Microsoft addressed CVE-2026-21513 as part of the February 2026 Patch Tuesday release. Organizations should apply this update immediately, prioritizing internet-facing systems, endpoints used by privileged users, and systems in government or defense environments.
Q: How do I know if my organization was already compromised before the patch was released?
A: Conduct a threat hunt focused on anomalous ShellExecuteExW invocations from MSHTML-related processes, DNS queries or connections to wellnesscaremed[.]com, and LNK files in unusual directories. Review endpoint telemetry for process lineage anomalies between late January and your patch application date.
Q: Is blocking LNK attachments sufficient to mitigate this vulnerability?
A: Blocking LNK file attachments at the email gateway reduces one confirmed delivery vector, but it does not fully mitigate the underlying MSHTML vulnerability. Akamai has noted that additional delivery mechanisms beyond LNK files may be viable, and the related CVE-2026-21509 Office vulnerability suggests a multi-vector campaign. Applying the official patch remains the only complete remediation.
Q: Why is APT28 still exploiting MSHTML if Internet Explorer is retired?
A: MSHTML was never fully removed from Windows — it remains embedded in numerous system components and third-party applications that use it as a rendering engine. This makes it an attractive persistent target for sophisticated threat actors like APT28, who specifically seek legacy components that receive less security scrutiny but still execute with significant system access.
Enjoyed this article?
Subscribe for more cybersecurity insights.
