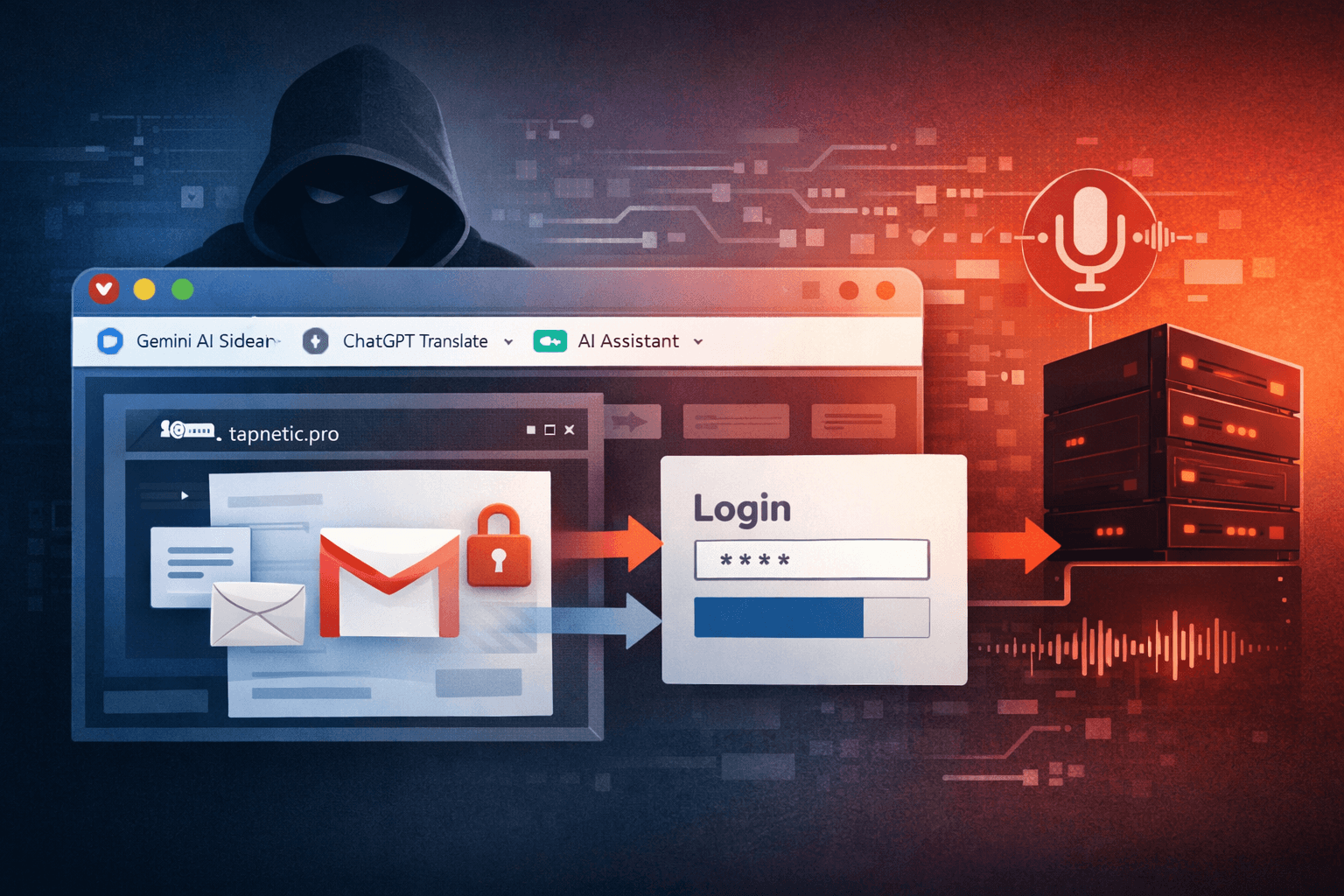
A sophisticated malware campaign dubbed AiFrame has compromised over 300,000 Chrome users through malicious browser extensions masquerading as AI assistants. Security researchers discovered a network of 30 fraudulent extensions sharing identical infrastructure and code, all designed to harvest credentials, extract Gmail content, and exfiltrate browsing data while appearing to provide legitimate AI-powered features.
This attack represents a dangerous evolution in browser-based threats. Unlike traditional extensions that rely on obvious malicious behavior, these imposters leverage the growing popularity of AI tools to gain user trust. The campaign's success demonstrates how threat actors exploit emerging technology trends to distribute malware at scale through official channels like the Chrome Web Store.
Understanding how these malicious extensions operate, what data they target, and how to protect your organization is critical for security teams navigating an increasingly complex threat landscape.
The AiFrame Campaign: Scale and Sophistication
Distribution Through Legitimate Channels
The malicious extensions infiltrated the Chrome Web Store by mimicking popular AI services. Extensions with names like "Gemini AI Sidebar," "AI Assistant," "ChatGPT Translate," and "Google Gemini" collectively attracted hundreds of thousands of installations before detection.
The most successful individual extension, "Gemini AI Sidebar," alone reached approximately 80,000 users before removal. However, numerous other extensions from the campaign remained available in the Chrome Web Store at the time of discovery, continuing to pose risks to unsuspecting users.
All 30 extensions share three critical characteristics:
- Identical underlying codebase with matching permissions
- Backend infrastructure routing to the domain
tapnetic[.]pro - Remote content loading capabilities that bypass Chrome's update review process
The Iframe Exploitation Technique
Rather than implementing AI features locally within the extension code, these malicious add-ons load content through full-screen iframes from remote domains controlled by the attackers. This architectural choice serves a strategic purpose beyond simple code efficiency.
By rendering functionality through remote iframes, the threat actors can modify the extension's behavior at any time without submitting updates through Chrome's review process. Once installed, the extension becomes a persistent backdoor that operators can reconfigure dynamically to execute new attack patterns or target different data types.
This technique effectively circumvents Chrome's security model, which relies on reviewing extension code before publication and updates. The reviewed code simply loads external content, making the actual malicious functionality invisible to automated and manual security checks.
Data Exfiltration Capabilities
Gmail Content Harvesting
Fifteen of the 30 extensions deploy specialized content scripts targeting Gmail specifically. These scripts inject at document_start on mail.google.com, ensuring they execute before the page fully loads and can establish hooks into Gmail's interface.
The malicious code performs several invasive operations:
- Injects UI elements that appear as legitimate Gmail features
- Reads visible email content directly from the DOM structure
- Repeatedly scrapes email thread text using
.textContentextraction - Captures draft emails before they are sent
- Intercepts user interactions with AI-assisted reply and summary features
When users activate what appear to be AI-powered Gmail enhancements, the extensions capture the email content along with contextual information and transmit everything to attacker-controlled servers. This approach bypasses Gmail's built-in security boundaries by operating within the user's authenticated browser session.
Table: Gmail Data Extraction Methods
| Technique | Target Data | Execution Timing |
|---|---|---|
| DOM scraping | Email thread content | Continuous during page view |
| UI injection | User interactions with emails | On feature activation |
| Draft monitoring | Unfinished email text | Real-time as user types |
| Context capture | Sender/recipient metadata | During email reading/composing |
Credential Theft and Session Hijacking
Beyond email content, the extensions leverage Mozilla's Readability library to extract page content from all websites users visit. This includes authentication pages where users enter credentials for various services.
The broad permissions requested by these extensions grant access to:
- Form data entered on login pages
- Session cookies and authentication tokens
- Saved password auto-fills triggered by the browser
- Two-factor authentication codes entered into web forms
By operating within the browser's trusted context, the extensions can capture credentials before they reach the target website's security controls. This positions them to intercept authentication data for corporate systems, cloud services, financial accounts, and any other web-based resource accessed through the compromised browser.
Audio Transcription via Web Speech API
The extensions possess the capability to remotely trigger voice recognition using the Web Speech API. When activated, this feature can capture and transcribe audio from the user's microphone, then transmit the transcripts back to the attackers' infrastructure.
The actual risk posed by this capability depends on the permissions granted during installation. However, if users approved microphone access—possibly believing it was necessary for AI voice assistant features—the extension could potentially capture:
- Confidential conversations occurring near the device
- Voice commands containing sensitive information
- Meeting discussions in remote work environments
- Verbal password disclosures or security questions
Technical Architecture and Infrastructure
Shared Backend Infrastructure
All 30 extensions route stolen data through a centralized backend infrastructure, with traffic directed to tapnetic[.]pro. This domain serves as the command-and-control (C2) hub for the entire operation, receiving exfiltrated data from all infected browsers.
The shared infrastructure reveals several important characteristics of the campaign:
- Centralized operation by a single threat actor or group
- Coordinated deployment suggesting automated extension generation
- Potential for cross-referencing data from multiple victims
- Single point of failure that could enable takedown efforts
From an attacker's perspective, this architecture enables efficient data collection and management. From a defender's viewpoint, it provides clear indicators of compromise (IOCs) that can be blocked at the network level.
Permission Abuse and User Deception
The extensions request extensive permissions during installation, justified by their purported AI assistant functionality. Users typically approve these permissions without scrutiny because they seem reasonable for the advertised features.
Table: Permission Requests vs. Actual Usage
| Permission Type | Stated Purpose | Actual Malicious Use |
|---|---|---|
| Read browsing history | Provide contextual AI assistance | Extract visited URLs and page content |
| Access data on all websites | Enable AI features across the web | Harvest credentials from login pages |
| Modify webpage content | Insert AI interface elements | Inject malicious scripts and data collectors |
| Communicate with remote servers | Process AI queries | Exfiltrate stolen data to C2 infrastructure |
This social engineering approach exploits user expectations. As AI tools increasingly require broad permissions to function, users have become conditioned to accept extensive access requests without questioning their necessity.
Detection and Response
Identifying Infected Systems
Security teams should immediately audit all Chrome browsers within their environment for the presence of malicious extensions. LayerX Security has published a comprehensive list of the 30 identified extensions and associated indicators of compromise.
Organizations can detect these threats through several methods:
- Reviewing installed extensions in Chrome's settings (
chrome://extensions) - Deploying browser management policies that inventory extensions
- Monitoring network traffic for connections to
tapnetic[.]pro - Analyzing browser extension manifests for suspicious permission combinations
Important: Extensions may use variations in naming and versioning to evade detection. Focus on identifying extensions that match the structural patterns and backend infrastructure rather than relying solely on name matching.
Immediate Remediation Steps
If any infected extensions are discovered, organizations should execute a coordinated response:
- Immediate removal of the malicious extension from all affected browsers
- Password resets for all accounts accessed from the compromised browser profile
- Session invalidation across all services to terminate any stolen authentication tokens
- Security audit of affected user accounts for unauthorized access or data exfiltration
- Network monitoring for continued connections to known malicious infrastructure
The password reset must cover all accounts, not just those directly targeted by the extensions. Since the malware could capture credentials from any authentication page visited during the infection period, assume comprehensive credential compromise.
Enterprise Browser Security Controls
Organizations can implement several preventive controls to mitigate the risk of malicious browser extensions:
- Deploy Chrome Enterprise policies that restrict extension installations to approved sources
- Implement allowlisting of vetted extensions rather than relying on blocklists
- Enable mandatory extension review and approval workflows before installation
- Configure security policies that limit extension permissions even when installed
- Deploy endpoint detection tools that monitor browser behavior and network connections
These controls create defense-in-depth layers that can detect and prevent similar attacks even when individual security measures fail.
Lessons from the AiFrame Campaign
The AI Trust Factor
This campaign succeeded largely because it exploited the current enthusiasm around AI technology. Users downloaded these extensions expecting to enhance their productivity with cutting-edge AI features, making them less suspicious of extensive permission requests.
The attackers understood that AI branding provides built-in justification for powerful capabilities. Voice recognition, content analysis, cross-site data access—all seem reasonable for an AI assistant, even though they create perfect conditions for surveillance malware.
Security awareness training must evolve to address this new threat vector. Users need guidance on evaluating AI tools critically, understanding that legitimate AI features don't require unrestricted access to all browsing data.
Browser Extension Supply Chain Risk
The Chrome Web Store, despite Google's review processes, proved insufficient to prevent this campaign's initial distribution. Several factors contributed to this security gap:
- Automated review systems struggle to detect malicious behavior implemented through remote content loading
- The volume of extension submissions overwhelms manual review capacity
- Extensions can appear benign during review, then activate malicious functionality post-approval
- Name squatting on popular AI brands creates user confusion and false legitimacy
Organizations cannot rely solely on marketplace vetting to ensure extension safety. Browser extension risk must be managed as a critical component of the broader supply chain security program.
Data Exfiltration Detection Challenges
Traditional security controls often fail to detect browser extension malware because the data exfiltration occurs within legitimate browser processes. The stolen data transmits through normal HTTPS connections that appear as routine web traffic.
Detection requires visibility into:
- Browser extension installation events and permission changes
- Unusual patterns of data access within browser contexts
- Network connections from browser processes to uncommon domains
- Volume and frequency of outbound data transfers
Security teams should evaluate security solutions that provide this level of visibility into browser-based threats, including browser isolation technologies and advanced endpoint detection capabilities.
Key Takeaways
- Over 300,000 users installed malicious Chrome extensions disguised as AI assistants, with the campaign remaining active through official distribution channels
- The AiFrame malware uses remote iframe loading to bypass Chrome's review process and dynamically modify behavior without detection
- Extensions specifically target Gmail content through DOM manipulation and UI injection, capturing emails, drafts, and user interactions
- Credential theft extends across all visited websites using the Readability library to extract form data from authentication pages
- Immediate remediation requires extension removal, comprehensive password resets, and security audits of affected accounts
- Organizations must implement browser security policies, extension allowlisting, and user awareness training focused on AI tool evaluation
Conclusion
The AiFrame campaign demonstrates how threat actors weaponize emerging technology trends to distribute malware at unprecedented scale. By exploiting user trust in AI assistants and the perceived legitimacy of official browser extension marketplaces, attackers achieved hundreds of thousands of installations before detection.
The technical sophistication of using remote iframe loading to bypass security reviews, combined with targeted Gmail content extraction and comprehensive credential harvesting, positions this campaign as a significant evolution in browser-based threats. Organizations face risks not just from the immediate data compromise, but from the precedent it sets for future attacks.
Security teams must recognize browser extensions as critical attack vectors requiring dedicated security controls, monitoring, and user awareness programs. The combination of restrictive installation policies, comprehensive detection capabilities, and educated users provides the most effective defense against these threats.
Frequently Asked Questions
Q: How can I check if my Chrome browser has any of these malicious extensions installed?
A: Navigate to chrome://extensions in Chrome to view all installed extensions. Cross-reference this list against the IOCs published by LayerX Security. Remove any extensions matching the AiFrame campaign, especially those with AI-related names from unknown publishers, and immediately reset passwords for all accounts accessed from that browser.
Q: If I removed the malicious extension, is my data still at risk?
A: Yes, data captured while the extension was installed may have been exfiltrated to attacker servers. You must reset passwords for all accounts, invalidate active sessions across services, and monitor for unauthorized access. Consider the period of infection as a full compromise window where credentials, emails, and browsing data were exposed.
Q: Why didn't Chrome's security detect these malicious extensions before I installed them?
A: The extensions used remote iframe loading to execute malicious code hosted outside the extension itself. Chrome's review process examines the extension code submitted to the Web Store, but cannot detect threats that dynamically load after installation. This technique allows attackers to pass initial security reviews and activate malicious behavior later.
Q: Can enterprise browser management tools prevent these types of attacks?
A: Yes, Chrome Enterprise policies allow organizations to restrict extension installations to approved allowlists, block installations from unknown publishers, and limit the permissions extensions can request. Combining these policies with network monitoring for suspicious C2 domains and user awareness training creates effective defense-in-depth against browser extension threats.
Q: What makes browser extensions particularly dangerous compared to other malware?
A: Browser extensions operate within the trusted browser context, giving them access to all data handled by the browser including credentials, session cookies, and page content. They run continuously while browsing and can intercept data before it reaches security controls. Unlike traditional malware, extensions are willingly installed by users and granted extensive permissions, making them difficult to detect with conventional security tools.
Enjoyed this article?
Subscribe for more cybersecurity insights.
